This article is more than 1 year old
'Diamondville' to shine as Intel's next Atom
Inside the 'Silverthorne' architecture
Intel executives admitted that Diamondville's clock speeds aren't directly comparable to those of the company's other mobile and desktop processors because all Atom chips have to process instructions in the sequence the commands appear in a program. This 'in order execution' contrasts with the 'out-of-order execution' technique employed by Merom, Penryn and other Intel CPUs to process whatever instructions they can, wherever they appear within a program. Silverthorne is Intel's first in-order CPU since the original Pentium. Its instruction processing pipeline is 16 steps long.
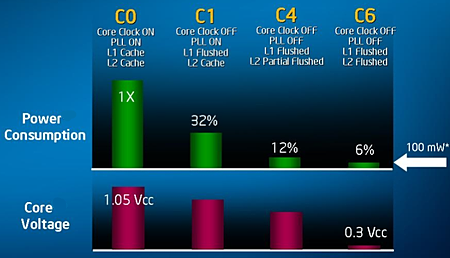
Power down: Silverthorne's sleep states
Out-of-order can boost performance because it means some instruction can be fed into CPU components that might otherwise be standing idle while another instruction is being dealt with. The upshot is that the chip can process more instructions in a give time, so it's faster. The cost is the complex circuitry needed to make this possible, circuitry missing from the Silverthorne and Diamondville architecture to keep the die size down.
To balance that, they use HyperThreading to try and keep otherwise un-utilised logic units occupied. How the absence of out-of-order and the presence of HT will balance out remains to be seen, so all we can say for now is that a 1.6GHz Atom N270 isn't necessarily going to be much faster than a 900MHz Celeron M - the Eee PC's processor - only that it probably will be. We'll have to wait for independently run benchmarks to find out for sure.
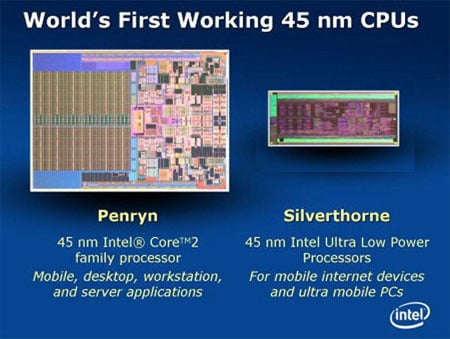
Silverthorne vs Penryn
For its part, Intel claimed this week that adding HyperThreading delivers a performance boost of around 37 per cent for an 18 per cent increase in power consumption when compared to a Silverthorne without HT running at the same clock speed.
The suggested chipsets mean Diamondville systems aren't going to be graphics powerhouses. With the emphasis on low costs, it seems unlikely that vendors will add in discrete GPUs to take over from the chipsets' GMA950 integrated graphics. If it happens, it'll be in desktops, but don't hold your breath.
Expect Diamondville to debut in June.
