This article is more than 1 year old
Has your shifty foreign neighbour got 16 mobes?
Call this number, sharpish
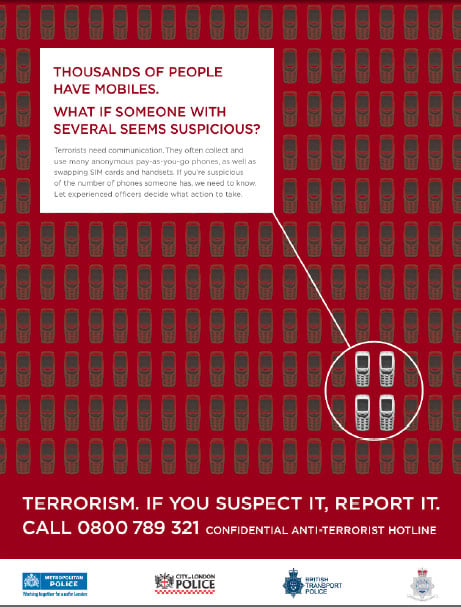
The Metropolitan Police have launched an intensive media onslaught aimed at advising Londoners just what to do if their shifty-looking Arab next door neighbour is packing mulitiple mobes, trading SIMs with the men in black turbans, taking delivery of binary liquid explosives, photographing CCTV cameras, or generally acting in a manner likely to undermine the security of the state:
The above poster forms part of a package of awareness-raising measures also including radio ads, postcards, and stickers, all pointing to the Anti-Terrorist Hotline on 0800 789 321.
Fair enough - up to a point. The transcript of the radio ad, which features "an individual thinking out loud about concerns she has around some suspicious behaviour", explains:
Female Voice over:
How d’you tell the difference between someone just video-ing a crowded place and someone who’s checking it out for a terrorist attack?How can you tell if someone’s buying unusual quantities of stuff for a good reason or if they’re planning to make a bomb?
What’s the difference between someone just hanging around and someone behaving suspiciously?
How can you tell if they’re a normal everyday person, or a terrorist?
Male voice over:
The answer is, you don’t have to.
That's right, just call the number and trained operatives will assess the threat, although we hope the threat-assessment criteria are rather more rigorous than they are in Stoke-on-Trent, where a garage mechanic recently enjoyed a spell in the cells after a member of the public mistook his MP3 player for a pistol.
And, of course, we're obliged to conclude with: "Hello, Anti-Terrorist Hotline? I've just seen a Brazilian bloke running down the Tube escalator. Can you send a team to shoot him or something?" ®