This article is more than 1 year old
Toshiba Portégé R500 slimline laptop
Not as sleek as the Air, but packs more features
Review Take this boy out of the box and the first thing you’re going to say — we guarantee it — is “strewth, that’s light”. We did. After years of carrying around small notebooks that were still big in weight, picking up this featherlight laptop was a real surprise.
OK, something as small as, say, the Asus Eee you expect not to weigh much, but a full-size machine? No way. Yet the R500 is a 12.1 in laptop with all the features you’d expect from any standard laptop, including a optical drive, built in and ready to use. Stitch that, MacBook Air…
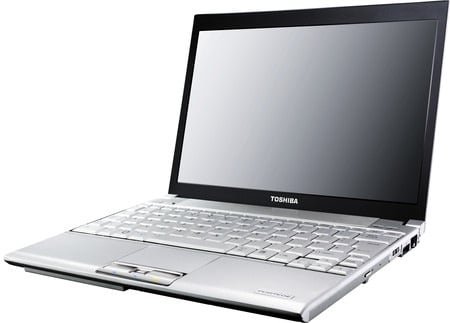
Toshiba’s R500: light
The R500 is certainly a well-connected machine. There’s a Gigabit Ethernet port on the right side of the machine next to one of the laptop’s three USB ports — the other two are on the left side, where you’ll also find a four-pin Firewire connector, mic and headphone sockets, and a VGA port. Turn back to the right of machine if you want to use its SD card slot, DVD writer and, tucked underneath, the PC Card slot.
You’ll also find a switch on the right side for the R500’s wireless links: it has 802.11b/g/n Wi-Fi — it’s a Centrino-branded laptop, so the wireless chippery is Intel’s — and Bluetooth on board.
The back of the R500 is pretty much all battery and it’s the R500’s thickest part. From there it slants gently to the front, where it finally curves quickly to a point. The contour’s symmetry is spoiled only by a bulge at the front, over on the left-hand side, that’s necessitated by some component that otherwise wouldn’t have fitted. The hard drive, probably.

Skinny
The wrist-rest area is also home to the R500’s built-in microphone — it’s over to the far left, right where your wrist is likely to be if you’re typing and talking at the same time — and the touchpad with its chrome-effect selection buttons and, between them, fingerprint reader. Shining through the chrome: an array of coloured icons for power, wireless status and so on.
