This article is more than 1 year old
Motorola calls up handset three-some
A sexy slider now Wi-Fi-enabled and two basic ringers
Mobile World Congress Wi-Fi’s the word according to Motorola: the handset manufacturer has unveiled its web-enabled MOTO Z6w phone, alongside the twin-like W161 and W181 handsets.
The MOTO Z6w slider provides 802.11 b/g Wi-Fi connectivity, in addition to quad-band GSM/GPRS/Edge cellular support. Its VoIP support, Motorola claims, means the phone’s able to switch calls seamlessly between either connection.
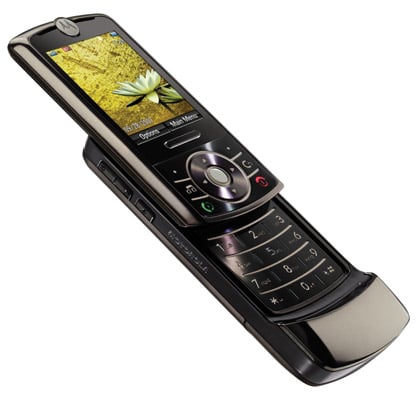
Motorola's Z6w slider - now with Wi-Fi
Windows Media Player is installed onto the Z6w to let you sing along to tracks stored in a variety of formats, such as AAC and MP3, on the phone’s 4GB micro SD card. You’ll also be able to put tracks onto the handset with ease, because a USB 2.0 port and Bluetooth connectivity are built in.
The phone has a 2in display and also features a two-megapixel camera, which captures video content at 14 frames per second.

Motorola's W161 (left) and W181 handsets
Motorola’s W161 and W181 handsets couldn’t be further removed from the Z6w, in terms of features. But while both candybar-esque devices look very similar to one another, the W161 only sports a black and white display.
Both are fairly basic phones, but the W181 has the upper hand because it sports a colour display, albeit with the same 128 x 128 proportions as the W161. It's also got 70KB of on-board storage, compared to the W181’s 20KB. Motorola’s made no mention of an external memory card slot on either handset.
Technology to ensure crystal-clear phone calls features on both the W161 and W181, as does FM radio broadcast reception.
You’ll have to wait until the second quarter of this year to get your handsets on the MOTO Z6w, whilst the W161 and W181 will both be released during the first quarter of 2008. No prices have been given yet.
Mobile World Congress 2008 Complete Coverage here
