This article is more than 1 year old
Forth Road Bridge hack redirects to smut bazaar
Firth and degradation
Updated Hackers turned the Forth Road Bridge website into a filth jamboree after breaking into its systems to plant script designed to redirect surfers to a Turkish site hosting malware.
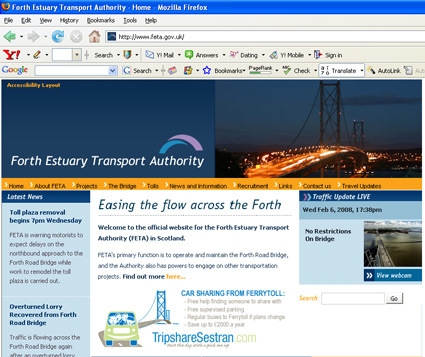
According to Scottish security outfit Roundtrip Solutions the website of the Forth Estuary Transport Authority (www.feta.gov.uk), which runs the famous suspension bridge in central Scotland, was hacked in order to serve up pop-up ads for porn sites. Roundtrip used AVG's LinkScanner security tool to determine that hackers were taking advantage of the (old and a little obscure) MDAC-RDS ActiveX exploit to launch an iFrame HTML element taken from a website under the control of hackers.
As a result users with unpatched Windows PCs visiting the site during the week or so before the problem was put right on 6 February were liable to end up with systems loaded with malware, according to an analysis by Roger Thompson of AVG's Exploit Prevention Labs. Both Roundtrip and Thompson, which assisted the Scottish firm in its analysis, reckon the Neosploit Hacking Toolkit was used to carry out the attack.
Analysis of the site revealed the exact mechanism of the ruse. "The exploit code was found fairly easily: the obfuscated JavaScript made it stand out like a sore thumb," Roundtrip reports. "This code made the browser connect to a server in Turkey with an IP address of 88.255.90.130. Most of the time this server returned instructions to look at the BBC website, but occasionally it delivered another JavaScript payload, which could have done anything it liked."
FETA took down the website soon after being notified of potential problems on Wednesday. The site was back online by late Wednesday afternoon, after it was rebuilt. "We took our website off-line for a few hours this [Wednesday] morning as a precautionary measure after a security breach on the servers of the external company that hosts the FETA website," a FETA spokesman explained. "The issue has now been resolved and the web hosting company is reviewing their security arrangements". ®
