This article is more than 1 year old
Intel Skulltrail high-end gaming system
Intel's showcase gets Nvidia SLI and AMD CrossFire
This means that Skulltrail effectively falls into two halves. On the one hand we have the dual Xeons and on the other we have the PCI Express graphics. There’s no denying that eight cores of Xeon power has the potential to be something special, and when we ran software that tests the CPU in isolation the results were staggering. POV-Ray 3.7 Beta 24, DivX 6.8 and iTunes 7.6 all churned through their work at a pace that left us stunned.
POV-Ray 3.7 Beta 24 Results
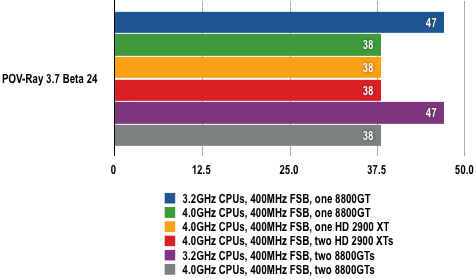
Times in Seconds
Shorter bars are better
At the standard 3.2GHz clock speed the Skulltrail system demolished POV-Ray in 47 seconds and when we overclocked to 4.0GHz the time dropped to 38 seconds. To put that in context, the V8 system with dual Xeons running at 3.0GHz took 1 minute 11 seconds and a Core 2 Q6600 2.4GHz took 2 minutes 51 seconds.
DivX 6.8 AVI Encoding Results
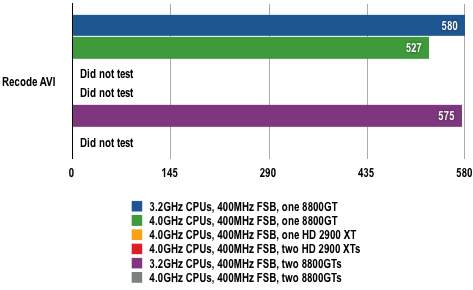
Times in Seconds
Shorter bars are better
iTunes MP3 Conversion Results
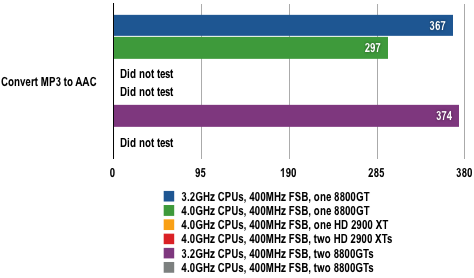
Times in Seconds
Shorter bars are better
