This article is more than 1 year old
Maxdata Belinea s.book 1 sub-notebook
Hard drive-equipped Eee killer?
We mentioned that the two machines' keyboards are the same size, but they're not identical. The s.book's is much more spongy, not so much in the key actions but because the whole board seems to have no solid underpinning. That's true of the Eee's keys too, but to a far lesser degree – you have to push very hard to make it dip in the middle and, unlike the s.book, it doesn't dip while you're typing.

Well-connected
Size-wise, the s.book is only slightly larger than the Eee, though it looks bigger, in part due to the odd screen positioning, but also because it has a chunkier design. The screen hinge is place further back from the keyboard than it is on the Eee, and with the gap between screen and lower section - handy for picking it up, this - it doesn't have the same cramped feel that the Asus does, even though there's barely any difference between the two machines' physical dimensions.
Where the Eee's casing is smooth and sloping, the s.book is all right angles. And it has gaps between its ports, which break up its straight lines and, ironically, make it look not less block-like but more so. The Belinea measures 230 x 171 x 29.4mm.
With the battery in place, it's 1.1kg and feels lighter then the similarly laden Eee, but then the s.book's battery has a capacity of just 2200mAh. At 4200mAh, the Eee's is almost double that. The official s.book runtime is three hours.
The Belinea comes with Windows' Power Options set to the Home/Office Desk power scheme set as default, but we re-set it to Portable/Laptop. We copied an H.264-encoded 640 x 360 video to the s.book's hard drive then set it running full screen and the screen set to maximum brightness to get an indication of battery performance.
Battery Life Results
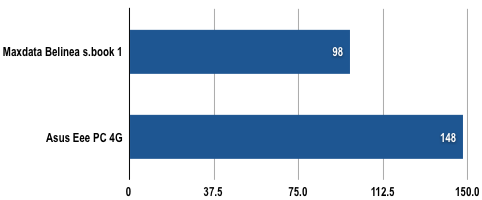
Battery duration in minutes
The s.book went into hibernation after 1 hour 38 minutes, whereas the Eee ran for 2 hours 28 minutes when displaying the same movie at the same settings.
