This article is more than 1 year old
The OLPC XO laptop
Is the mean, green thing hacker-friendly?
Multimedia
Multimedia is the XO's weakest area. As shipped, it's unusable for multimedia applications.
The supplied open source Gnash Flash player doesn't play YouTube videos. After replacing it with Adobe's own Flash Player, the videos played, but were choppy to the point of being unwatchable.
If the default browser is used, there will be two video windows on each page, with the top one saying "Flash: click to play". Meanwhile, the bottom one is already playing, but you have to scroll down to see it.
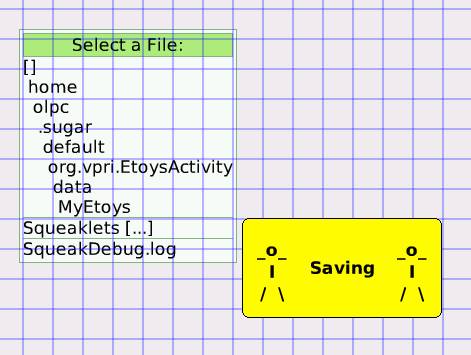
Opening a MP3 file in the Journal launches the Etoys activity. Playback skips intermittently, and stops playing altogether if the focus is switched to another activity. If the XO does manage to complete playing a song, it will give an error saying the file location has changed. The XO will then crash and take a while saving, although what is being saved isn't clear. After the crash, the MP3 filename changes to 'Etoys activity' and can't be played. The file isn't really corrupted, but the USB or SD card must be removed and remounted to fix the file association and make it playable again.
This is a mess, and looks like this:
Opening an Ogg file launches the browser by default. It displays a visualisation which is clearly too much for the XO's CPU, and the sound skips. If Etoys is used to open the file, it has the same problems as it does when playing MP3s.