This article is more than 1 year old
Sony Ericsson touts talker trio
Two Walkman phones and a clamshell
CES Sony Ericsson has gone on the handset offensive and launched two music-orientated handsets, alongside an extra clamshell just for luck.
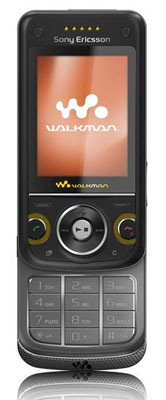
W760 when open
The W760 slider and W350 both fall under its Walkman brand and include many of the established musical features from its existing handsets, such as TrackID and Mega Bass. They also support MP3 and AAC files.
However, the W760 always pips the W350’s features to the post in virtually every arena. For example, both have Bluetooth connectivity, but only the W760 has A2DP for wireless streaming, built-in stereo speakers and SensMe, which Sony Ericsson claims helps you to select tracks suiting your mood.

The W350 has a keypad cover
While the W350 may have a fairly basic 1.3-megapixel camera, the W760 is a slightly more powerful 3.2-megapixel offering. Being Sony handsets though, each uses Memory Stick Micro cards for their picture and data storage, with the W350 shipping with a 512MB card and the W760 a 1GB card.
SE’s chosen to carve up each handset’s GSM band connectivity too, giving users the option of 900/1800/1900Mhz band frequency operation with Edge support on the W350 and quad-band GSM connectivity with its rival. The W760 also has HSDPA for speedy downloads though.
If neither really takes your fancy, then SE also launched the tri-band GSM/GPRS/Edge-ebabled clamshell Z555, which looks much like NEC’s N704iμ handset and has a 1.3-megapixel camera with 4x digital zoom onboard.
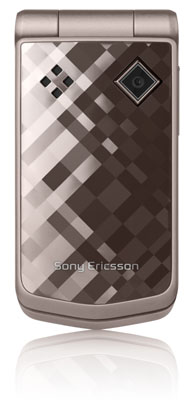
Z555: shiny
Like the W760, it too features Bluetooth with A2DP. However, because it doesn’t fall under the Walkman banner, users don’t benefit from anything spectacular in terms of musical capabilities.
The Z555’s most unique feature is called Gesture Control, which enables users to mute an incoming call or snooze its alarm just by waving their hand over its front.
SE’s W760 and W350 will be available in the second quarter of this year, while the Z55 will be released at some point in the first quarter. Prices for any of the three handsets haven’t been released yet.
