This article is more than 1 year old
Nvidia nForce 780i SLI chipset
PCIe 2.0 and Penryn - bring 'em on
The layout of the Asus is very conventional with the power connectors and six laid-down SATA connectors at the edge of the board. If you use two or three graphics cards then the expansion options vanish as the board will be full of graphics and if you don’t want to run SLI then it’s hard to see why you’d choose either a 680i or 780i motherboard in the first place.
Considering the high-end nature of the P5N-T Deluxe it’s a surprise that you only get four USB ports on the I/O panel however there are two more ports on a bracket and provided you have some front-mounted USB ports on your case then all should be well. The SoundMAX integrated audio with digital outputs is a decent choice but remember, you’re supposed to be using this motherboard with up to three graphics cards so the chances of using an X-Fi could be limited.
There are a couple of bits missing that we’d expect to see on a high-end Nvidia board such as Power and Reset micro buttons, a debug display and a second Gigabit LAN port.
3DMark06 Results
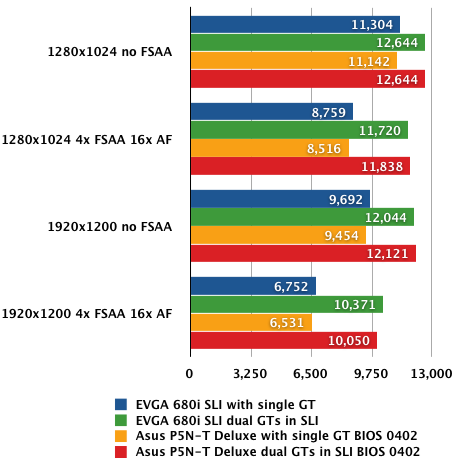
Longer bars are better
We tested the two boards with a Core 2 Duo E6750 and 2GB of Kingston DDR2-800 memory with a pair of GeForce 8800 GT graphics cards running on Windows Vista Ultimate Edition. If we had three GTX or Ultra cards you can bet we’d have used them as Asus includes a 3-way SLI bridge in the package but we don’t and neither, let’s face it, do you.
Crysis Results
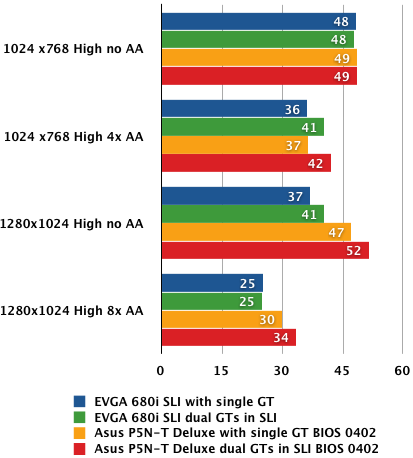
Average frame rates
Longer bars are better
In the main we couldn’t separate the performance of the two platforms although the 780i SLI leapt ahead in Crysis at a resolution of 1280 x 1024. It’s most unlikely this is a direct benefit of the new chipset so for the time being let’s call it a quirk of the drivers.
F.E.A.R Extraction Point Results
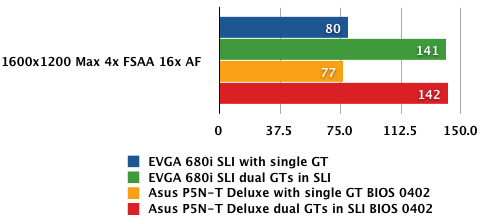
Average frame rates
Longer bars are better
