Mind the Gap Saturday Mind the Gap Saturday is a feature every Saturday where Blognation China tells its readership the differences - the gap - in the tech, mobile and enterprise worlds between China and the Western World.
You thought Blogging was addictive, bad, or <fill in the blank here>? Get a load of microblogging. If blogging chained you to your Mac or PC, microblogging will chain you to your humble mobile phone.
But just how active is microblogging in the People's Republic? And how do people tweet along - do they use Twitter or a local equivalent? Find out more on this Mind the Gap Saturday.
C2C?
The PRC redefines another acronym - in this case, C2C. Nope, it's not customer to customer, it's Copy to China.
If you've been surfing around, you sometimes may have noticed that the Chinese web is full of stuff that looks like it was copied from the West. This phenomenon (C2C) is there because China's a big marketplace, and someone just has to get something "foreign" to 1.3 billion (well, at least to the wired 172 million and counting).
The potential customers - and the potential cash - all await He Who Comes First. It's probably not rocket science, then, that they all scramble for the gold. Lost in the gold rush is this thing called innovation. And that's why we have sites looking very similar to their American counterparts.
Tweeting to a familiar tune
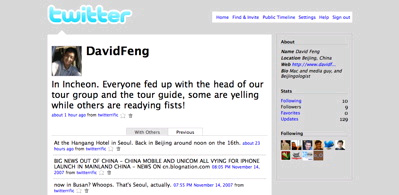
However, Twitter and its local variant Jiwai.de look quite different. Let's start with a look at Twitter. The beat's always there - someone is updating something just about every last second.
If you're not Twittering along, you might start to wonder: Who the heck is interested in what I'm doing? Once you're Twittering along, though, there's no way out. I've used it both as a notification system and as a semi-propaganda machine: when the world seemed to go totally wrong this morning, I aired my complaints (in Chinese no less) about how bad the world has become. Those who subscribed received about two or three posts in traditional Chinese (apologies if you don't understand what I'm on about).
Twitter is useful in another way: It's great as a notification system. Suppose you've got your friends all Twittering along, and they're at the airport waiting for you. A quick tweet will let them know if your flight's delayed or not (you of course, text tweet before you board the plane), and they'll get the message - on their Macs (or PCs) or on their mobiles.
Twitter this, Twitter that
