Bell was finally able to put Shockley's junction transistor mass production in 1952, and afterwards licensed the design to other firms too, most notably a new, small Japanese company called Sony. Two years later, Bell replaced the germanium used in its transistors with silicon.
Shockley, Bardeen and Brattain won the Nobel Prize for Physics "for their researches on semiconductors and their discovery of the transistor effect" in 1956, almost two years after their work resulted in the release of the first transistor radio.

From Bell to Nobel: Shockley, Bardeen and Brattain
These early transistors were used primarily to amplify an analog signal, which they were better able to achieve - certainly in a much smaller space - than circuits based on thermionic valves. Only much later, after Jack Kilby (1923-2005) and Robert Noyce (1927-1990) combined transistors into the first integrated circuit chip, in 1958, did the potential in the transistor's ability to operate as a switch begin to be realised.
Transistors operating as current switches could be combined to form logic gates, and the basic foundations of modern digital circuitry were born. Put a number of these gates together into an integrated circuit and you have the basis for a computer. Put enough of them together and you have a microprocessor, which Intel released in 1971 as the 2300-transistor 4004.
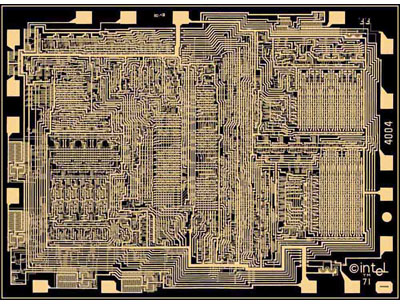
Intel's 4004: 2300 transistors on board
These days, processors contain hundreds of millions of transistors, making up their maths units, control systems and on-board memory banks.
