This article is more than 1 year old
Nvidia G92-based GeForce 8800 GTS 512MB
The 8800 GT and then some
Review The GeForce 8800 GT slipped into Nvidia’s line-up towards the top of the range by offering similar performance to the existing 8800 GTS with 320MB of memory. This was achieved with an updated version of the 'G80' chip called 'G92', which moved the fabrication process to 65nm, changed the memory controller, raised the core speed and increased the number of unified shaders - or Stream Processors.
Although the 8800 GT performed in a similar way to the 8800 GTS it used a different technical approach and employed a different design. Where 8800 GTS and GTX are double-slot designs that blow cooling air over a hefty heatsink and out through a vented bracket at the back of the case, the new GT has a single-slot form-factor and keeps the air inside the case of your PC.
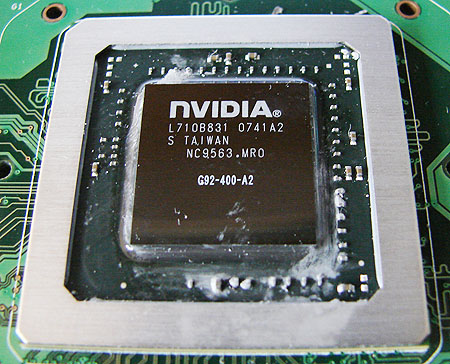
Nvidia's GeForce 8800 GTS: the G92 version
As we mentioned in our review, the GT gets hot to the touch, and we’ve recently heard a rumour that explains this situation. Nvidia was determined that the new GT would beat AMD’s equally new ATI Radeon HD 3870 so it raised the core and memory speeds as far as it dared and then set the fan speed to the point where it would just about keep the GT cool. The result is an impressive level of performance from a quiet, slender graphics card at a very keen price. The 8800 GT looks like a natural to replace the existing 8800 GTS over the next few months.
Which makes Nvidia’s new 8800 GTS something of a puzzle. For one thing, there’s the name. There is only one GT, so it’s clear that you’re getting a G92 chip. But the new GTS sits alongside existing GTS models that use the G80 chip. The safest way to tell them apart is that G80 cards have either 320MB or 640MB of memory while the G92 version comes with 512MB of GDDR 3. And a 256MB model is coming soon to further muddy the waters.
The technical differences between the new GTS and the GT are very slight and come down to clock speeds as they have the same amount of memory, the same memory controller and - according to most card suppliers - they each have 112 Stream Processors.
