This article is more than 1 year old
Al Gore climate change site hacked
Penis pill outrage
A blog on a site promoting Al Gore's climate change documentary, An Inconvenient Truth, has been hacked by penis pill-promoting spammers.
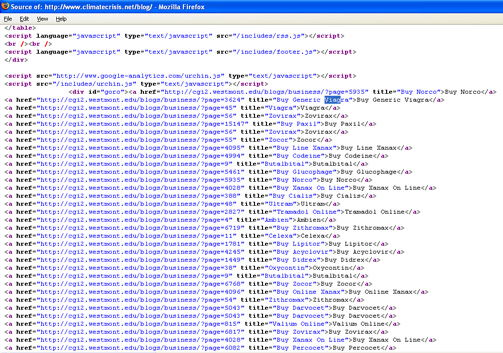
Links on the blog portion of the climatecrisis.net site point to websites hawking online pharmaceuticals in an apparent bid by miscreants to promote their search engine rankings. The links, not apparent to a casual observer but clearly visible in the page source, promote drugs including Viagra and Xanax.
The approach is a more aggressive variant of comment spam attacks, which involve posting links to dodgy sites on blogs. Search engines, such as Google, give priority to sites linked to from popular web destinations, such as the climatecrisis.net domain. Spammers and their hacking accomplices try to take advantage of this behaviour in order to illicitly gain higher places in search page rankings.
In the case of the climatecrisis.net hack, the links point to pages on a site hosted by Westmont College, a small Christian college in California, that's also fallen victim to hackers.
Only the blog section of climatecrisis.net seems to have been affected by the attack. The techniques used in the assault remain unclear, although researchers at Sunbelt Software told IDG that exploiting vulns in the WordPress Web publishing software used by both Westmont College and the Inconvenient Truth blog was the likely avenue of attack.
Sys admins on climatecrisis.net are yet to purge the offending links at the time of writing.
Former vice-president Al "I invented the internet" Gore, who became a Nobel prize laureate and Oscar winner thanks to the success of An Inconvenient Truth, was unavailable for comment. ®
