This article is more than 1 year old
Sony Ericsson ‘invents’ drag-and-drop for handhelds
'Point and flick' file transfer
Sony Ericsson has applied for a patent that, if granted, would give it ownership of a data-transfer method for portable devices which allows users to send files from one device to another with the flick of a finger.
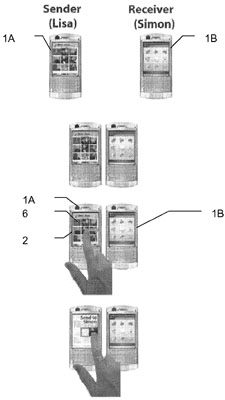
Lisa selects a file on-screen and flicks it to Simon
Recently released documents describe how data, such as MP3 files, can be selected on-screen and then ‘flicked’ - using a touchscreen-detected gesture, or a gadget's joystick - in the direction of another compatible device to initiate an automatic data transfer over a short distance.
It sounds a little like virtual catch, but with text documents, photos, music files and so on.
The patent application, filed with the US Patent and Trademark Office in March 2006 but updated last week, seems biased towards mobile phones, but it's general enough to take in handheld games consoles, and music and media players.
Sony Ericsson is equally broad-minded - why tie yourself down? - when it comes to short-range transmission technology. It reckons the technique is as applicable to today's Bluetooth and yesterday's infra-red as it does to future near-field commmunications (NFC) systems.
What the application doesn't cover in detail is how the system gains its directionality. That's easy with line-of-sight technologies like infra-red, but for Bluetooth, the system would need to be able to detect which recipients the source device is 'pointing' at and then remove from the list any that aren't paired with the source or authorised to accept files from it.
We wish Sony Ericsson luck, but we're minded of Sony's original notion behind its Memory Stick card format: that the card could pick up and drop off data by literally tapping files presented on PCs' screens.
That technique never made it out of Sony's labs, and we wonder if Sony Ericsson's 'flick'n'file' system will either.
