This article is more than 1 year old
Nokia 6110 Navigator GPS phone
Gets you from A to B without going via L, O, S or T
More Route 66 maps covering other countries can be added, and you can sign up for additional services too – such as live traffic updates, safety camera alerts, weather reports and Lonely Planet travel guides.
Another neat extra is the ability to send screenshots of some navigation maps as MMS messages or emails to any other mobile phone user - very useful if someone’s struggling to find you when you’re both out and about, or for arranging meetings. You can also send them short-range via Bluetooth.
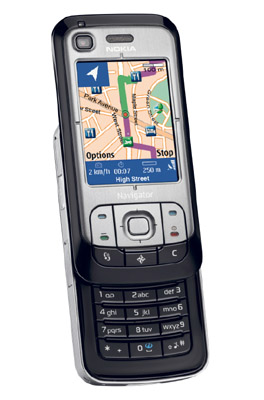
A functional key layout
Similarly, you can send step-by-step navigation instructions in written form via texts, MMS or email. Longer routes will require multiple text messages, so it's usually cheaper to send an MMS.
We made extensive use of the 6110’s sat nav functionality and were very impressed with the system. One serious issue, though, is battery life. The GPS system eats through the battery, so we’d suggest investing using a car charger for longer journeys. It’s easy to leave GPS running in the background too, so be careful exiting the application properly to save on juice.
Aside from the sat nav system, the 6110 puts in a solid, assured smartphone performance. The menu navigation controls will be familiar to any Nokia S60 user. The standby page has quick access icons ranged across the top, and the main menu button delivers you into a pack of application and folder icons arranged in grid formation - this can be altered into a carousel-style presentation. Clicking on these takes you into applications or folders with more sub-menu options.
With 3G and HSDPA giving respectable download speeds, surfing using the Nokia Browser is a decent experience. It uses Mini Map overviews of pages to help you find your way around, and can tailor views of pages to be optimised for a mobile screen. You can also store RSS links. Downloads of audio and video content are zippy – mere seconds for full-length music tracks from mobile network portals.
