This article is more than 1 year old
Asus Eee PC 4G sub-sub-notebook
The ultimate laptop?
If the keyboard's hard to use because it's small, that goes double for the twee touchpad. A mere 45 x 30mm, it's got a scroll space over on the right-hand side, but that just makes it ever fiddlier to use.
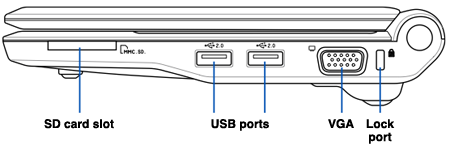
Right-hand side port array
Below the pad are the mouse buttons, both formed from a single, flat piece of plastic. Asus could at least have sculpted the single piece to make it easier to hit the bit of the bar you want. We fould ourselves hitting it too close to the middle, often doing a left-click when we wanted a right one. And pushing the button with one hand while controlling the cursor with the other – to select a block of text, for example - is a recipe for tying your fingers in knots.
We'd suggest you just take a travel mouse with you.
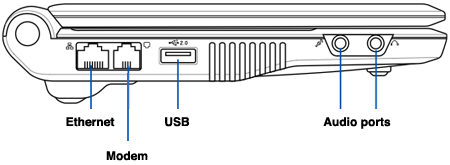
Left-hand side port array
The 701 has three USB ports for this: one on the left side; the others on the right, between the Eee PC's VGA port and its SD/SDHC card slot. The other side is home to 3.5mm headphone and microphone sockets, a 10/100Mb/s Ethernet port and – for us – a blocked modem port. The 4GB 701's 5200mAh battery plugs into the back of the machine next to the power port, and there's a microphone located right at the front of the machine, below the mouse button.
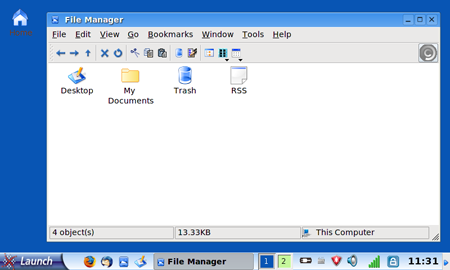
A standard desktop is a basic hack away
Turn the Eee PC over and there's a large cover. If you're willing to invalidate your warranty, you can open it up to expose the memory slot - the 701 has a 512MB 400MHz DDR 2 DIMM in place already, but it'll take a 1GB module - and the expansion bay. The latter is presumably where the anticipated 3G connectivity module will go.
Closed, the 701 measures 225 x 165 x 25-35mm, but in real terms that means it's the size of a typical hardback novel. It weighs about the same too, but if you want a more specific figure, it's 890g. In other words, eminently portable, and a perfect size to close up and stash away in your backpack or briefcase when you've finished surfing, writing the latest chapter of your magnum opus or whatever.
