This article is more than 1 year old
Canon Ixus 860 IS compact camera
Another hit from Canon?
Review Behavioural scientists reckon that, within ten seconds of meeting someone for the first time, we’ve already decided whether we like them or not. Well, if the Canon Ixus 860 IS was a person, we would have liked them from the moment we first clapped eyes on them.
It’s a handsome thing, with smooth curves, a two-tone silver and black finish, and feels reassuringly solid in the hand. The rear of the camera is dominated by a large, 3in LCD screen composed of 230,000 pixels. Images displayed on the screen are sharp and clearly defined. On top of the body is a small slider button for selecting camera, scene or movie modes, a tiny power button and a zoom rocker control.
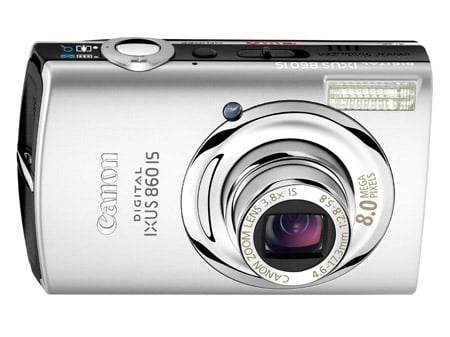
Canon's Ixus 860 IS: sexy beast
Around the back is the ubiquitous multi-function controller, along with buttons for playback, direct printing, menu selection and display mode. Hidden behind a (rather flimsy) plastic flap is a mini USB port and an AV socket, while underneath the camera is another flap, this time concealing the battery and SD card slots.
You get the usual assortment of accessories - connecting leads, battery charger, and PDF manual and software on a CD. Canon also throws in an SD card as the Ixus 860 has no internal memory. With memory prices so low these days, it was disappointing to find Canon providing a measly 32MB card, which will record just eight images at the highest resolution or 14 seconds of moving pictures.

The LCD's nice and big
When it comes to features, the 860 IS offers quite a lot. There’s an eight-megapixel CCD fed through a 3.8x optical zoom lens equivalent to 28-105mm on a 35mm camera, allowing users to pull in extra detail from the side. You also get a 4x digital zoom; shutter speeds from 15s to 1/1600 of a second; ISO ratings from 80 to 1600; a variety of shooting modes, including auto, manual (although not manual exposure), Stitch Assist, and scenes such as Night, Kids and Pets, Snow, Beach and Underwater. Of course, the last one of those should probably only be used in addition to the optional underwater protective cover...
