This article is more than 1 year old
T-Mobile Sidekick Slide messaging phone
Still doesn't quite cut it with kids
With the screen up, the dinky keys are fine for tapping out text with your thumbs, though go carefully if you have thicker digits. One gripe is the additional, alternative characters, all too small and too blue against the black keys, making it almost impossible to identify them in low-light conditions.
To type out phone numbers, as well as a row of number keys, there's a secondary keypad-style grid of numbers overlaid onto some of the letter keys. You can call also use a virtual numberic pad on screen when the slide is closed.
Feels like a PDA not a phone
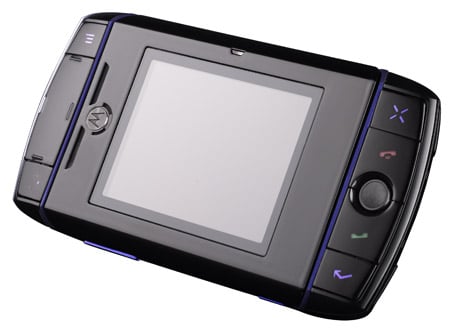
You navigate the main menu control using a neat trackball on the right of the keyboard. Or you can use the four-way pad on the left side. Icon-labelled buttons in each corner allow you to backtrack or go straight to the main menu screen. There are shortcut buttons on the top of the phone too for the camera and messaging options. Call and End keys take care of making voice calls.
The main menu is a carousel of large icons which shows what each one does as you highlight the options in turn. Roll over the messaging and organiser icons, and you'll also be shown if you have any unread messages, notes, tasks or events to look at. Click on these and you either get a sub-menu carousel or go straight to the function you’ve selected.
The colourful, user-friendly graphics and background don’t always extend to the business end of the features. Some, like message composition and calendar input, are presented straight, like they would be on a regular PDA.
Finding extra options for each page requires you to tap a button on the top left of the device. Drop-down menus often give you a wide range of choices, but without, say, a regular Options soft-menu, it’s not always obvious when additional options are available. Numerous shortcuts can be used in many of the functions, such as the browser, using multiple alphanumeric and function key combinations - though these aren’t usually intuitive. You’d have to spend plenty of time and effort learning them.
On registering the device, you can set up an email account with a [username]@sidekick.t-mobile.co.uk address. You can also add up to three personal POP3 email accounts to the device, so you can get your email pushed directly to the Sidekick as they arrive in your other in-boxes.
