This article is more than 1 year old
Motorola Razr 2 V8 mobile phone
Cutting... er... edge
The Razr 2 comes in two versions, with 512MB or 2GB internal storage - our review sample had 512MB. The downside is there’s no additional memory card expansion. D’oh. With 2GB Micro SD cards for mobiles now widely available for under £15, we’re sure most people would easily prefer the flexibility offered by swappable cards.
The external screen puts many a mobile’s main display to shame
The music player can take tracks easily from a PC using the supplied USB cable. Songs can be copied over with Windows Media Player 11 or simply dragged and dropped into the phone if you change the phone’s USB setting. MP3, AAC, AAC+, WAV, WMA and Real Audio file formats are all supported.
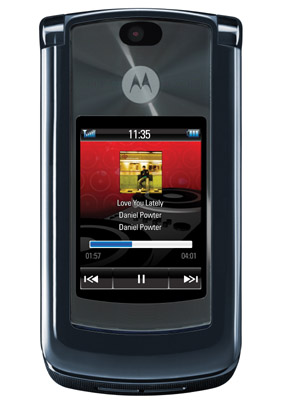
The player itself offers plenty of regular MP3 player options to arrange music. When the phone’s open, the navigation pad controls play, but close the lid and that external display comes into effect. You get track details on screen, and the bottom section of the screen provides touch-sensitive play/pause, forward and backward keys - with a handy bit of vibrating feedback to let you know they’ve been pressed. You can’t explore all the music player app's options from the outside, however.
Volume keys are positioned on the side of the phone, and you can lock the external music keys by a long press of a button under the volume rocker. Incidentally, the same key also doubles up as a camera activation key and to select functions when the phone’s open.
The music player performs well, with the external speaker loud enough to scare fellow commuters - but alas still prone to typical mobile tinniness. The supplied stereo handsfree headset is adequate for casual listening. Motorola uses the mini USB port as the headphone socket, so there’s no plugging in better-quality headphones. And you can’t charge and listen with headphones at the same time – unless you go the stereo Bluetooth route.
