This article is more than 1 year old
Sony Ericsson Walkman W660i music phone
3G makeover
There's a key to engage the camera on the side of the W660i, along with volume controls that also operate the camera's zoom. The W660i’s Memory Stick Micro (aka M2) card slot is on the side too, so you can hot-swap cards easily. A 512MB card is bundled in the box.
The W660i uses Sony Ericsson’s regular menu set-up: a grid of icons, each of which takes you into lists of options. Sub-menus are presented as a single page of options or a series of tabbed multi-page panels. Despite plenty of configuration choices and a healthy amount of functionality inside, the menu system manages to avoid overwhelming with complexity; you see what you need to see on an uncluttered display, and it’s intuitive to use.
The mic module has a 3.5mm jack connector so you can plug in other headphones
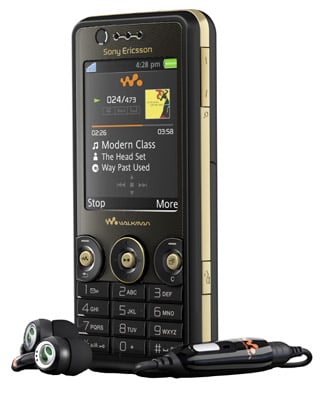
Sony Ericsson kits out its Walkman phones with strong add-ons in the box, including decent quality stereo headsets and generous-sized memory cards. The W660i package also comes with the regulation two-piece Walkman handsfree kit. A proprietary connector clicks into the base of the phone, with a 3.5mm jack connector midway on the in-line mic module, so you can also plug in other standard headphones.
The audio performance through the supplied headphones was very impressive, clear and precise, with plenty of bass response without having to tweak the phone’s equaliser settings or trigger the Mega Bass option.
The Walkman 2.0 music player provides a slick platform for listening to tunes. It supports MP3, AAC, AAC+, eAAC+, WMA and AMR file formats. The user interface is detailed and sophisticated-looking, including support for album cover art. When activated, the phone's navigation pad becomes the Walkman control panel.
The Walkman player uses a neat graphic icon-chain to show where you are in the menus when scrolling through your tunes from the My Music menu. Options include artist, album, track and playlist listings, while there are one-touch links to Sony Ericsson’s online downloads site or a network-based online music store, if you’re using a network-locked version of the W660i.
