This article is more than 1 year old
MS, Mitsubishi tout translucent touchscreen concept
Apple got there first?
From the Archive And it sounded such a smart idea too. Microsoft and Mitsubishi are developing a 'translucent' touchscreen. The idea: touching the back of the panel controls user interface elements displayed on the front. Cute, but the question to be asked is: where do all the electronics go?
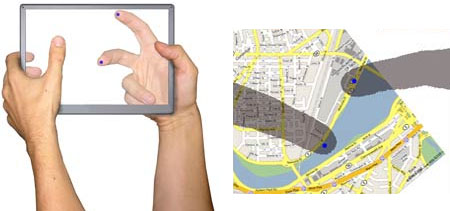
Apple's 'translucent' iPod panel patent (left) and Microsoft/Mitsubishi's 'translucent' touchscreen concept
The two companies call the system LucidTouch, MIT Technology Review reports. As the picture shows, the notion behind LucidTouch is the ability to hold the panel in two hands and still control it. Today's touchpanels, by contrast, require users to hold them with one hand, and point and click with the other.
The translucency in the concept is real, but in the prototype screen the two companies have built it's virtual: a webcam on the back feeds the main display, its image being mirrored to look right when it's shown on the front of the panel.
LucidTouch also operates like a standard touch panel, so users can still interact with the screen in the usual way.
The snag here is clear - literally. Today's handheld touchpanels sit on top of a whole mess of electronics - processors, hard drives, memory, system logic and so on - all of which are going to have to be crammed into the display's bezel if Microsoft and Mitsubishi are ever to get the concept off the ground. The prototype sweeps such complications under the virtual rug of a desktop PC.
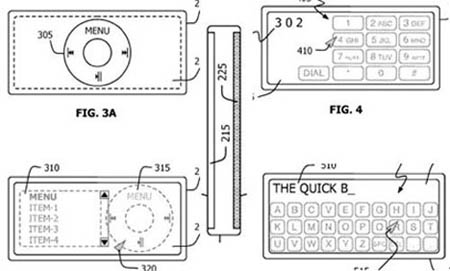
Apple's 'translucent' iPod panel patent
Microsoft and Mitsubishi aren't alone in conceptualising such a system. Earlier this year, it emerged that Apple has filed a patent application the details a similar approach to allow, say, an iPod owner to control the device one-handed, manipulating virtual controls displayed on the front of the player either by touching them directly or by tapping the back of the device with an index finger.
