This article is more than 1 year old
Techies blast big media over copyright warnings
More like copywrong warning, am I right? I'll get my coat
A trade group that includes Google, Microsoft, Yahoo! and other big names in tech is asking federal regulators to clean up allegedly misleading language in copyright warnings.
The Computer & Communications Industry Association announced today it has filed a complaint with the Federal Trade Commission on behalf of consumers. The trade group claims that several corporations have misled the public for years by misrepresenting their rights through warnings that include "deceptive and threatening statements."
The complaint was filed against Major League Baseball, the National Football League, NBC/Univeral, DreamWorks, Harcourt Inc. and Penguin Group.
“Every one of us has seen or heard that copyright warning at the beginning of a sports game, DVD or book,” said CCIA CEO Ed Black, during a press conference at the National Press Club. “These corporations use these warnings not to educate their consumers, but to intimidate them.”
The complaint asks the FTC to flatten the current language in copyright warnings, and launch a campaign to educate consumers of their rights under fair use laws.
According to the CCIA, some copyright holders threaten criminal and civil penalties against consumers exercising constitutionally guaranteed rights. Therefore the warnings violate the FTC's mandate against unfair or deceptive practices in commerce.
"There is nothing unlawful, untruthful, or inaccurate about the warning labels on our movies, which adhere to long accepted legal standards and are nearly identical to the warnings used by some of CCIA's own members," NBC/Universal said in a statement.
The CCIA maintains the overreaching warnings reduce demand for new and innovative products and services in digital media. Consumers are confused about their rights to legally acquire the media, and avoid products out of confusion or fear, the group claims. ®
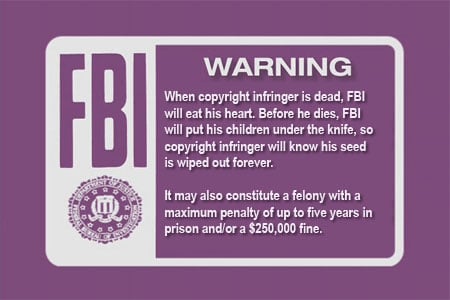
Some allege the warnings are worded a bit strongly.
