This article is more than 1 year old
Computer program to take on the Unabomber
Man vs. Machine challenge
How intelligent is a computer - and just what does it mean to be intelligent, anyway?
The Association for the Advancement of Artificial Intelligence (AAAI) aims to clarify that question with its Man vs. Machine Poker Challenge, taking place today and tomorrow in Vancouver, British Columbia.
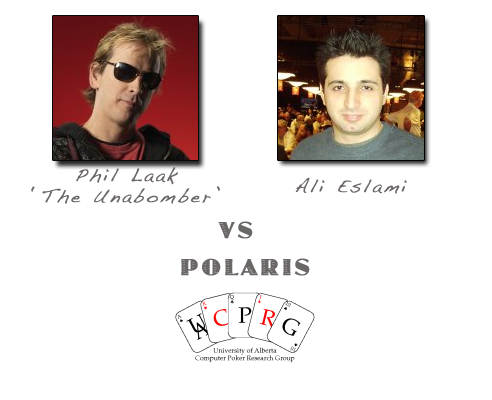
Polaris, a poker program developed at the Computer Poker Research Group of the University of Alberta, will compete against poker professionals Phil “The Unabomber” Laak and Ali Eslami in a two day Texas Hold’em tournament designed to test the limits of computer “thought” in real world scenarios.
Part of the challenge for proponents of artificial intelligence lies in the difficulty of defining exactly what intelligence is: “intelligence” as we typically understand it is a rather haphazard measurement of our abilities, some of which lend themselves to duplication via computer software, and some of which do not. Human intelligence is as much about communication and nuance as it is about performing mathematical functions, which is all that computers are really good at. Computers, in short, excel at the purely computational tasks that lend themselves to ready measurement, which is why within the closed universe of the chessboard computers are capable of beating even the greatest human players.
On the other hand, computers do miserably at the forms of emotional intelligence that define so much of what we are as human beings. Poker - a game of imperfect information, with its potent mixture of probability and human psychology – is the kind of talent that in the past has humbled even the most powerful supercomputers.
Polaris seeks to redress that imbalance.
Two copies of the program will compete as a team against the two professionals in a version of duplicate poker, a poker variant designed to minimize the element of chance. In duplicate poker, players at different tables play the same hand and compete not against those at their own table, but against those playing the same hand at different tables. Luck is still involved, inasmuch as no one can predict the behavior of the other table’s opponents, but the game is largely one of skill, which is why it has slipped under the radar of the ever-vigilant American authorities.
In the Man vs. Machine Poker Challenge, each teammate will play the hand of his teammate’s opponent, and teammates are forbidden to communicate with each other during the match. The match should therefore provide a fairly accurate gauge of the relative skill of each individual player, and provide at least a glimpse of just how much of that emotional intelligence can be coded into computer program. It should also provide insight into the hotly debated topic of the degree to which skillful poker play consists of an understanding of numeric probability and how much is sheer bluff.
Imperfect information characterizes the world in which we live, and the development of a computer capable of functioning at a high level at a poker table would be a major breakthrough for the artificial intelligence community, with implications far beyond the gambling world.
My money’s on the Unabomber.®
Burke Hansen, attorney at large, heads a San Francisco law office
