This article is more than 1 year old
The IBM ThinkPad: 15 years old today
The iconic black laptop celebrates its birthday
On 16 June 1993, Big Blue announced the ThinkPad 500, described at the time as its first sub-notebook. Retailing for $1999 and measuring 25.3 x 18.8 x 4cm, it was based on a 50MHz 486SLC2 processor and offered with a choice of 85MB or 170MB hard drive - for an extra $500. The AC adaptor was built in to allow the 500 to be connected directly to the mains, saving users from having to lug around a power brick too.
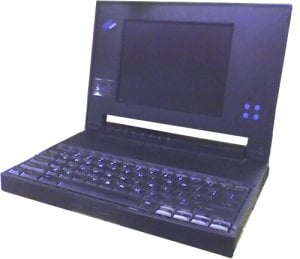
IBM's ThinkPad 500: its first sub-notebook
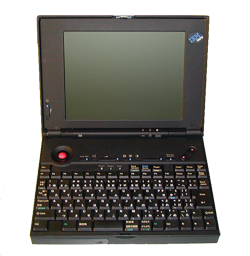
The 350 and 350C built on the original 300, upping the CPU to a 25MHz 486SL from the earlier machine's 386-class chip and increasing the choice of storage capacities to 125MB and 250MB. The two 350s cost $1999 and $2499, while the two 350Cs were priced at 2599 and 2999.
1993 and the years to come would see further tweaks to these models, alongside some curious variations: the ThinkPad 220 compact sub-notebook in 1993, followed by the 800 series of PowerPC-based laptops in 1995. That year also saw the introduction of the ThinkPad PC110, handheld PC only made available to Japanese buyers.


IBM's PC110: the first palmtop ThinkPad
The PC110 was based around a 4.7in 640 x 480 passive matrix colour display and featured a 33MHz 486-class processor, 20MB of memory and an internal 4MB Flash card for permanent storage. It also had a 2.4Kbps modem. It even had side-mounted LCD strip to display battery status information and the like.
IBM's ThinkPad 220: its first sub-sub-notebook
The 220 was also intended for Asian buyers. Measuring 22.6 x 16.6 x 3.2cm, it packed in a 16MHz 386SL processor, 2MB of memory, an 80MB hard drive, a PCMCIA slot and a 7.7in 640 x 480 display. It was powered by six AA batteries.
More Forgotten Tech...
• 15 years ago: the first mass-produced GSM phone
• Compact Disc: 25 years old today
• From 1981: the World's first UMPC
• Apple's first handheld: the Newton MessagePad
• Atari's Portfolio: the world's first palmtop
• 'Timna' - Intel's first system-on-a-chip
• BeOS: the Mac OS X might-have-been
• Sony's first Mylo
