This article is more than 1 year old
Facebook found pimping crudware
Serves up ads for deceptive security software
Facebook has become the latest website to be found pushing services that deliver highly deceptive security warnings designed to trick users into buying software.
Purveyors of this scam are making use of Facebook Flyers, small ads that get posted on Facebook pages associated with a specific region. At 5,000 impressions for just $10, it's a bargain.
We spotted a Flyer targeted at Facebook users in the San Francisco region that purportedly advertised a dating service. When clicked, the ad delivered a warning that our machine could be infected. Those who click through are taken to a site for a product called Malware Alarm which informs their machine is "infected with spyware!" The site then urges the user to download Malware Alarm.
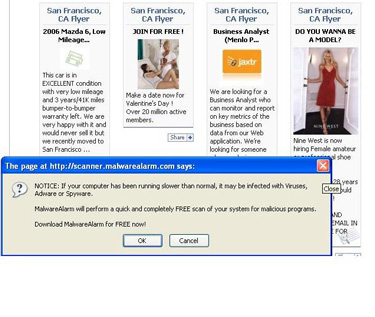
Clicking on the Flyer that says "Join for Free" brings up this popup. The warning is part of a scam designed to trick Facebook users into buying unneeded security software.
Security vendors say Malware Alarm's free version gives bogus security warnings designed to con end users into buying a premium version of the program. The software has been reported to flag common Windows files and innocuous programs as malware.
Facebook isn't the only site that's been found to push such "crudware," as we've come to call programs such as Malware Alarm. Last week, a security researcher's blog hosted on Blogspot was found to also found to redirect users to a site associated with Malware Alarm. MSN and MySpace have also been found promoting the programs, which also go by the term scareware.
While there are no reports showing Malware Alarm steals passwords, sends out spam or engages in other malicious activity, the program is considered a pariah in security circles. The ability of its purveyors to infiltrate Facebook's advertising system raises questions about what else may be slipping through the cracks at the social networking site.
We contacted a Facebook representative to see if they were even aware of the problem but didn't get a response. ®
