This article is more than 1 year old
Sonnet Tempo SATA Express 34 ExpressCard eSATA adaptor
Add-in eSATA ports for laptop Macs
Next, after connecting up the WD MyBook, we used Mac OS X's Disk Utility application to format both drives using the OS' own journaled file system and then to connect the two as a RAID 0 array, presenting both drives as a single 931.27GB unit, with data chunks alternately written on one drive then the other, a technique called 'striping'.
Multi-drive eSATA tests
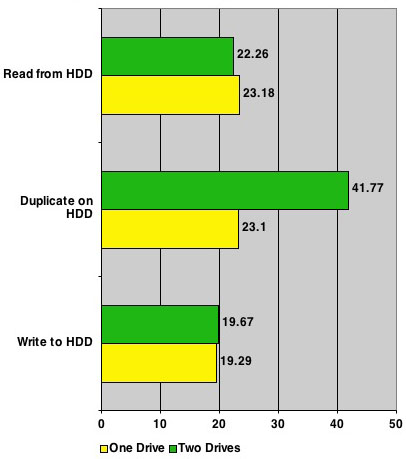
Results in MBps - longer bars are better
Writing data to the drives and reading it back yielded comparable numbers to the single drive, reflecting the limits of the MacBook's own hard drive. But look at what a difference duplicating data on the external drive set made: using RAID almost doubled the bandwidth. Photoshop users, imagine what that could do for your Scratch Disk usage?
We used Retouch Artists' Photoshop Speed Test action to try it out. Running the actions on a 2142 x 1449 RGB image using the MacBook Pro's hard drive only took 206.63s. Restarting Photoshop CS1 this time using RAID array as the Scratch Disk saw the action run time fall to 172.75s, a 16.4 per cent reduction.
Some Mac users will, not unreasonably, claim they don't need eSATA because Firewire 800 does the trick. That may be true for now, but as Apple showed with its first MacBook Pros, Firewire 800 isn't a given. It's not widely supported beyond the Mac niche, whereas we're seeing eSATA on more and more high-speed external drives and on PCs. eSATA is going to become cheaper - Firewire 800 isn't.
Future-proofing your MacBook Pro - or ExpressCard-equipped PC, if doesn't have an eSATA port of its own - will set you back around £95, not a bad price to pay. It's not for everyone - most of us can make do with Firewire 400 and USB 2.0 for a few more years until Macs get built-in eSATA ports.
Verdict
Want to take advantage of eSATA and RAID on your MacBook Pro? Sonnet's Tempo SATA Express 34 is an easy way to make it happen.

