In our recent mobile state of the nation survey, we asked you about what was important in a mobile device. In many respects, the results were pretty predictable in that, surprise surprise, battery life and decent voice capability were top of the list:
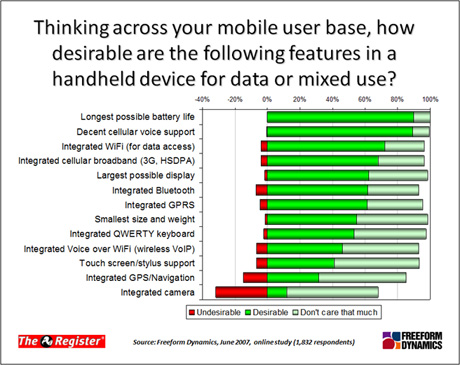
Quite a few then highlighted the importance of high-speed data access, whether WiFi or cellular based, with a fairly consistent shout beyond this for a reasonably sized display and basics such as integrated Bluetooth support.
As you work your way down the list, however, you get to features and functionality such as QWERTY keyboards, Wireless VoIP, etc, that appeal to some, with others not being that fussed. Then at the bottom we have a couple of items that not only appeal to a minority, but are actively not wanted by some people. Indeed, there are more people that definitely don’t want an integrated camera than want one, though the majority can’t get worked up either way.
This variation in demand for features begs the question of how organisations decide which of their mobile users are issued with which types of device – or even, whether the organisation decides at all, as there is clearly the option of leaving the decision in the hands of users themselves.
Against this background, we'd like to know how it works in your organisation. Which way do you lean on the freedom versus control thing and why? If you like to lock everything down, how do you decide which users get which devices? If you try to stike a balance, then what approach do you use - standard range of devices from which the user can chooose, or anything so long as it conforms to a certain spec or list of criteria? And how easy is it to enforce whatever policies you have in place given that users often think of their device as something very personal?
We know a lot of you have had to tackle the issues in this whole area, so tell us your experiences, good or bad, below:
