This article is more than 1 year old
Sentient world: war games on the grandest scale
Sim Strife
In fact, Homeland Security and the Defense Department are already using SEAS to simulate crises on the US mainland.
The Joint Innovation and Experimentation Directorate of the US Joint Forces Command (JFCOM-J9) in April began working with Homeland Security and multinational forces over "Noble Resolve 07", a homeland defense experiment.
In August, the agencies will shift their crises scenarios from the East Coast to the Pacific theatre.
JFCOM-J9 completed another test of SEAS last year. Called Urban Resolve, the experiment projected warfare scenarios for Baghdad in 2015, eight years from now.
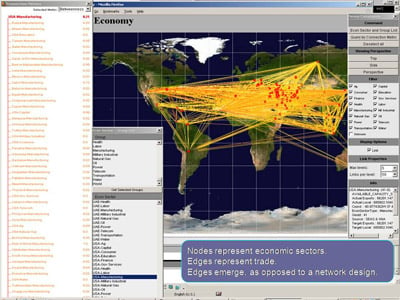
JFCOM-9 is now capable of running real-time simulations for up to 62 nations, including Iraq, Afghanistan, and China. The simulations gobble up breaking news, census data, economic indicators, and climactic events in the real world, along with proprietary information such as military intelligence.
Military and intel officials can introduce fictitious agents into the simulations (such as a spike in unemployment, for example) to gauge their destabilising effects on a population.
Officials can also "inject an earthquake or a tsunami and observe their impacts (on a society)", Chaturvedi added.
Jim Blank, modelling and simulation division chief at JFCOM-J9, declined to discuss the specific routines military commanders are running in the Iraq and Afghanistan computer models. He did say SEAS might help officers determine where to position snipers in a city square, or to envision scenarios that might emerge from widespread civil unrest.
SEAS helps commanders consider the multitude of variables and outcomes possible in urban warfare, said Blank.
"Future wars will be asymetric in nature. They will be more non-kinetic, with the center of gravity being a population."
The Iraq and Afghanistan computer models are the most highly developed and complex of the 62 available to JFCOM-J9. Each has about five million individual nodes representing things such as hospitals, mosques, pipelines, and people.
The other SEAS models are far less detailed, encompassing only a few thousand nodes altogether, Blank said.
Feeding a whole-Earth simulation will be a colossal challenge.
"(SWS) is a hungry beast," Blank said. "A lot of data will be required to make this thing even credible."
