This article is more than 1 year old
Levi's announces mobile phone
But is it pre-shrunk?
First Prada, now Levi's. The jeans maker is to launch a mobile phone, it said this week, but the doyenne of demin is remaining tight-lipped about many of the device's capabilites.
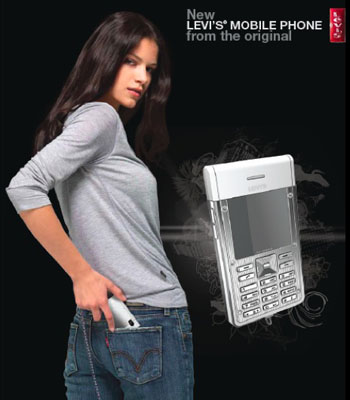
Levi's Phone: iPod white for the ladies...
Dubbed simply the Levi's Phone, the device will be manufactured under licence by the Paris-based ModeLabs. While a denim-covered version has yet to be announced, the steel-framed Levi's Phone will appear with "shiny silver" and "shiny sand" finishes for the ladies, and "metallic silver", black and "brown copper" for the lads.
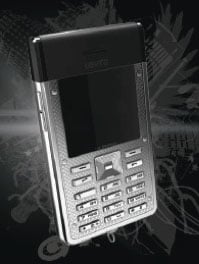
...and a darker model for the gents
Levi's will also include a detachable chain on the phone, certainly a draw for the rockers, skaters or those a little too worried about pickpockets. Unfortunatly, Levi's only said that its phone will enable users - or, more specifically, "young people" - to "connect, enjoy music, and exchange images and videos whilst on the go".
Some online reports are suggesting that it will include Bluetooth and an MP3 player - not exactly out-of-blue guesses, we'd say.
The Levi's Phone will be available in Europe from September, but pricing details are yet to be released.
