This article is more than 1 year old
SanDisk 4GB Micro SDHC memory card
Tiny form-factor, big storage capacity
Testing yielded average write, copy and read data transfer speeds of 4.46MBps, 3.21MBps and 8.87MBps, respectively. As you can see from the chart, that compares well with the 4GB SanDisk SDHC card I tried out back in December 2006. Both cards were tested in the same USB 2.0 port on a MacBook Pro, connected through the same SanDisk MicroMate SDHC-compatible card reader. SanDisk's 512MB Ultra II SD card still has the edge on write speed.
Memory card test results
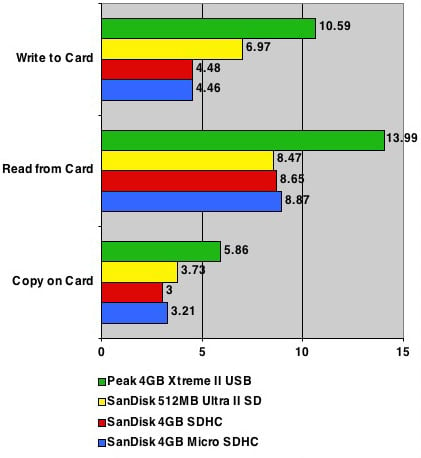
Speed ratings in MBps - longer bars are better
Of course, you can now get 2GB Ultra II SD cards, and 4GB Extreme III SDHCs if you want the highest SD card speeds and capacities. But then the Micro SDHC card isn't really an alternative to these. While you might use SD cards as an alternative to USB Flash drives, you're probably not going to want to do so with the Micro SDHC - if you're going to be using it in an SD-sized sleeve, whether with a USB adaptor or not, you may as well just buy an SD card and have done with it.

SanDisk's 4GB Micro SD card and adaptor
No, the Micro SDHC is best left to the handsets it was designed for, and as we mentioned that's a very limited number right now. If you're a Nokia N95 owner, the SanDisk card is the best, if not the only way to expand you're handset's storage capacity. More devices will come, so the 4GB card is going to find more homes in future.
Verdict
SanDisk's 4GB Micro SDHC card isn't going to replace your favourite USB Flash drive, but it's arrival is very good news for owners of the few devices that support the Micro SDHC specification. The card offers plenty of storage at a reasonable price.

