This article is more than 1 year old
Intel power PC platforms: Core 2 Extreme QX6800 and V8
Blistering performance?
Review Intel has been dancing all over AMD's financials with its Core 2 processors for the past year and it's keeping up the pressure, most recently with the Core 2 Extreme QX6800 and, more intriguingly, it's product-that-isn't-a-product, the V8 platform.
Intel's V8: firing on all cylinders?
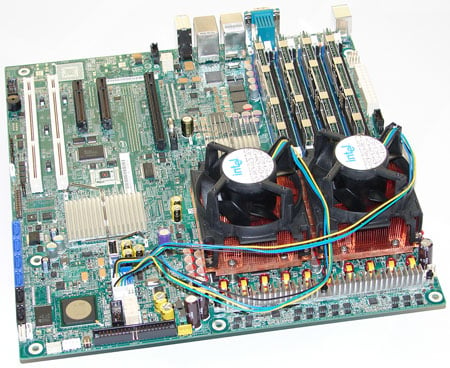
Let's start with V8 as it's something of an odd ball. It consists of an Intel S5000XVN ATX motherboard and two quad-core Xeon X5365 processors, each clocked to 3GHz and capable of operating on a 1333MHz frontside bus. With it, Intel sent us a pair of CPU coolers, 4GB of Samsung FB-DIMM PC2-5300F memory and an 850W power supply from Cooler Master.
So, that's eight physical cores on two sockets all with an estimated value of £2400. Good value as a bundle? It's hard to be sure, as Intel isn't selling the V8 as a system but is instead touting it as a technology showcase.
Or is it? As it happens the Xeon X5365 processor isn't currently available through the usual channels. If you want one, you have to buy a Mac Pro from Apple. The covering letter that came with the V8 refers to an "eight-core media creation PC", which is a pretty good description of the top-of-the-range Mac Pro.
Could V8, or a version of it, be a board supplied by Intel for Apple and now getting a lease of life beyond the Mac platform? Neither Intel nor Apple are saying, of course.
