This article is more than 1 year old
Finding missing galaxies: Spitzer triumphs again
No word on how they were lost
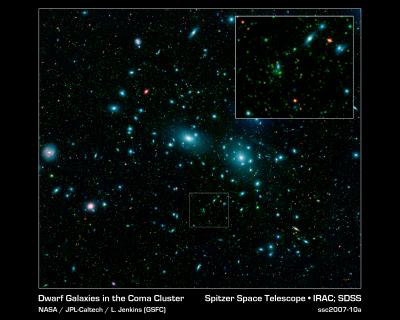
NASA's Spitzer observatory has logged more than 1,000 previously unknown dwarf galaxies hiding out in a giant cluster of galaxies.
Using data from the infrared observatory, a team led by Leigh Jenkins and Ann Hornschemeier, both at NASA Space Flight Centre, was able to resolve many galaxies that are too faint for other telescopes to see.
Dwarf galaxies are thought to be the earliest stage of galactic evolution, and provide the building blocks for larger galaxies. Researchers also use them as tracers to track the larger scale structure of the universe.
But for all their usefulness, they have been remarkably thin on the ground. Simulations suggest we should find more of them in giant clusters, like the coma cluster, than have been seen to date.
The coma cluster, as it is known, lies 320 million light years away in the (surprise!) constellation Coma. It spans a volume approximately 20 million light years across, and holds hundreds of galaxies that have already been studied.
As a giant cluster it should be positively brimming with dwarf galaxies. And it seems it is. Of 30,000 objects logged by the research team, 1,200 were found (on closer examination) to be dwarf galaxies. Scaling up to take in the whole cluster, this implies at least 4,000 dwarf galaxies.
The team had initially thought that some of the fainter objects would be background galaxies even further away. But secondary data from the William Herschel telescope settled it: the faint smudges were small galaxies - with masses comparable to, or even smaller than, that of the Small Magellanic Cloud, one of the Milky Way's satellite galaxies.
"With Spitzer's superb capabilities, we have suddenly been able to detect thousands of faint galaxies that weren't seen before," says Jenkins.
"We're blowing away previous infrared surveys of nearby clusters," Hornschemeier notes. "Thanks to Spitzer, we can observe nearby clusters such as Coma very deeply in a short amount of time. The total observing time is comparable to just a few nights at a ground-based observatory."
The research is being presented at the American Astronomical Society meeting in Hawaii. The discovery paper will also appear in the Astrophysical Journal, NASA says. ®
