This article is more than 1 year old
Phishers add call forwarding to their arsenal
The evolution continues
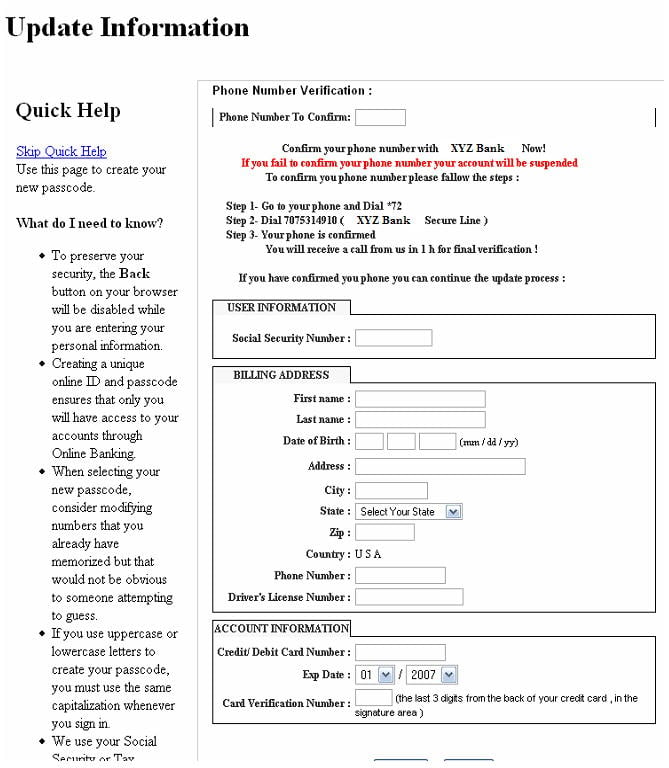
The folks at SecureWorks have observed a new phishing technique that uses call forwarding to route a victim's incoming phone calls to a number controlled by the attacker.
Victims are told to confirm their phone number with their bank by dialing *72 followed by a series of numbers. In the US, the sequence will cause most phones to forward all incoming calls. Once completed, the victim hears a message saying the confirmation has been successful.
The call-forwarding ruse is included in a more traditional phishing email that attempts to dupe victims into divulging credit card information and personal identification details. Successful phishing attempts allow the attackers to use the victim's credit card, then provide the victim's identification credentials in the event a banking representative calls to confirm the transaction. ®