This article is more than 1 year old
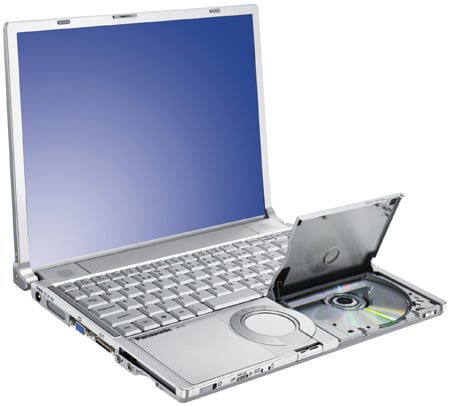
Panasonic CF-Y5 Toughbook laptop
A Navy SEAL of notebooks... a lumberjack of laptops
Review The CF-Y5 sits at the executive end of its Toughbook range, which if you're actually a stubble-sporting, rugged type, is realistically nearer the bottom of any table of toughness. So you won't be able to drop it down a crevice in the Antarctic and still expect to send an email.
But if you fancy yourself as one among the more extreme of the executive elite, you'll be able to safely throw it on the back seat of your Ford Mondeo with careless abandon and still successfully send an email.
As the Toughbook is the only brand of laptop Panasonic makes, you'll find the rugged bits developed for the top-end titles soon trickle down to the lighter, less reinforced models. Thus making the executive range of the Toughbook series considerably more resilient in comparison to most other laptops: you can drop it from about 15 inches or spill a glass of water over the keyboard without voiding your warranty.
And it can withstand about 100kg of force - roughly the weight of a middle-aged sales executive...as long as he distributes his weight evenly. (However, the manufacturer recommends that if you do want to stand on your Toughbook, you should place a book on it first.)
There is actually a quite unusual reason why the Y5 and Panasonic's other executive Toughbooks (the T5 and W5) were built to withstand 100kg. Apparently, Japanese customers were complaining that the Tokyo underground trains were so packed full of passengers that their laptops were literally buckling under the pressure. So engineers went to investigate armed with a pressure gauge in a shoulder bag and discovered that on a typical journey they were getting their noses pressed against the window with about 70kg of rush-hour force. Thus it was set as the benchmark. True story.
