This article is more than 1 year old
Cluster spies turbulent reconnection
Plasma is as plasma does
New data from the European Space Agency's Cluster satellites show a magnetic reconnection event taking place, even in the turbulent plasma around our planet.
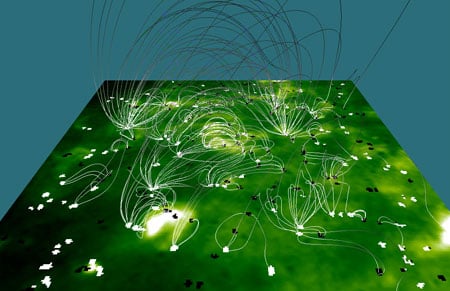
Magnetic reconnection happens when magnetic field lines reconfigure themselves: breaking and reconnecting with other nearby field lines.
The phenomenon can be found in various stellar phenomena: star formation, solar explosions and it has even been linked to the entry of solar material into the Earth's atmosphere. On a larger scale, reconnection has also been observed at the boundary of our solar system and interstellar space.
It has also been predicted, by computer modelling, that it would take place in turbulent plasma environments, but until now had never been observed.
Cluster - a constellation of four satellites, went looking for the phenomenon in the magnetosheath, one of the most turbulent plasma environments in the solar system.The magnetosheath lies just inside the bow shock wave created by the solar wind when it hits the Earth's magnetic field.
They discovered that during a reconnection event, the local plasma is accelerated and heated. The researchers say the work could explain how the sun creates high energy particles.
It might have practical implications for those trying to dissipate energy in fusion devices, and will also be useful for those studying the activity of our sun, particularly solar flares. ®
