This article is more than 1 year old
A monkey hanger's guide to Net Neutrality
El Reg goes Westminster
Descriptions of the internet reflect all kind of fears and utopian fantasies - and take many shapes. You can play this game too.
However, when we need to draw inferences, for the purposes of public policy, or to write laws or regulations, we need to be precise with our metaphors
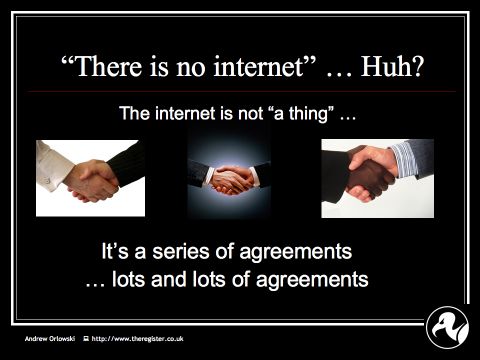
The first thing to remember is that there is no ONE internet.
That's because the internet is a way of getting lots of very different networks to talk to each other.
In effect, the internet is thousands and thousands of private agreements.
And this diversity has a local flavour. It reflects market dynamics today - very specific to the UK.
It reflects our own unique history of innovation, deployment, and regulation. And, of course, it reflects local needs: what do we want from computer networks?
So our networks reflect heterogeneity and diversity.
"Neutrality" became a hot topic in the United States last year, because AT&T and Verizon are deploying high speed networks for delivering a TV competitor to cable. They needed to enhance the network, because today's internet doesn't do what they want. The "agreements" aren't sophisticated enough to guarantee good video across network boundaries.
New applications, such as Bittorrent and Joost, abuse the "Honour box", where everyone agrees to play nicely.
But it isn't just about TV. New applications such as real time video monitoring in healthcare can't be done reliably as they should, because of the problems with today's internet.
Neutrality is emotive, but unfortunately the voice of technical experts hasn't been heard - until recently.