This article is more than 1 year old
Sony Vaio VGN-UX1XN ultra-mobile PC
Think of the smallest laptop you've ever seen, and this will be smaller
Review The Sony UX1XN is quite possibly one of the smallest laptops ever. Think of the smallest laptop you've ever seen, and this will be smaller. Probably. Everything about it is dinky - it's barely bigger than a thick-ish paperback book, yet it packs a full Vista-touting PC inside its diddy dimensions.
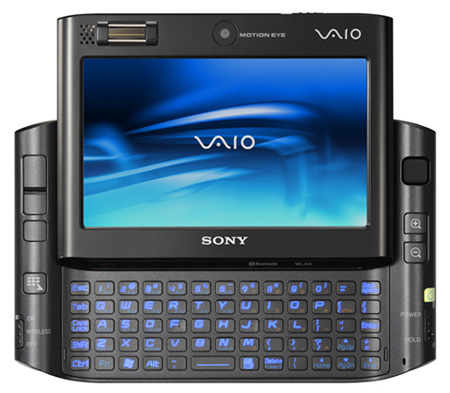
Sony's UX series has been around in Japan for some time, only available on these shores via unofficial import. The UX1XN - UX1 for short - is the first model to be officially supported over here and it's fully kitted out with Windows Vista Business too. All in a machine that measures just 15 x 9.5 x 3.5cm and weighs a mere 500g.
While you'd expect a machine this size to make a compromise here or there, Vista capability isn't one of the corners that has been cut. The Intel GMA 950 graphics chip has enough grunt to run Vista's whizzy Aero interface, so you get the full Vista experience despite its small size.
Vista pegs its Windows Experience Index score at 2.7, with the 3D graphics holding it back - the overall score is determined by the lowest component score. Across the categories it gets 2.9 for processor, 4.3 for memory, 3.2 for graphics, 2.7 for gaming graphics and 5.2 for hard disk.
While the scores aren't huge - they are impressive given the UX1's small size. Running it through PCMark05 it only managed to pull in a score of 1636, which is pretty low.
The Intel Core Solo U1500 processor, running at 1.33GHz, is nothing special and 1GB of DDR 2 memory is fairly standard. Where Sony has pulled out the stops, however, is with the hard drive. At first glance 32GB seems a bit measly, but this isn't any old 32GB model - it's a Flash drive. This has two advantages: it's faster than a standard drive and it's also more durable since there are no moving parts. While you should still treat UX1 carefully, it's going to be more resilient to the odd bump or two than a device with a traditional spinning hard drive.
