Austrian manufacturer Nanoident Technologies today cut the ribbon on the world's first factory that literally prints opto-electronic sensor circuitry and components onto virtually any surface, including plastic, ceramic and silicon.
The Linz plant operates like a giant inkjet printer. The semiconductor is made of up of conjugated polymers and nanoparticles sprayed onto a substrate in a pattern that creates the circuitry layout. Some of the new sensors are 100sm thick. Others are just ten atoms wide. To give you an idea of the scale, a human hair is 50,000nm thick.
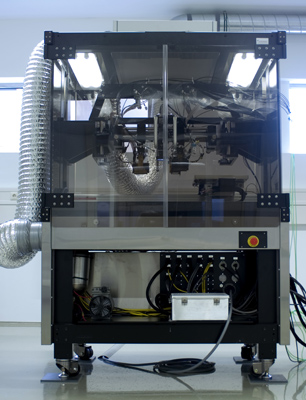
A Nanoident circuitry printer unit
Nanoident's printing method means that virtually any material can be 'printed' on. The substance used can be rigid or flexible, flat or curved, thick or as thin as 20 micrometres - one-fifth the thickness of standard 80gsm paper. Once dry, the structural integrity of the printed material is tested to ensure it's up to the standard needed for use.
Unlike silicon components that often result in waste by-products, the materials used in this new method of production are not damaging to the environment, Nanoident claimed. Because the construction process has to be very precise, no unnecessary product over-matter is manufactured.
Nanoident also claimed the 'ink' is absolutely 100 per cent environmentally friendly. The nanoparticles, for example, are manufactured from silver and contain no additional dangerous or hazardous chemicals, it said. But because these semiconductors are actually so very, very small, the disposal of any product using these components actually depends on how the whole product is disposed of.
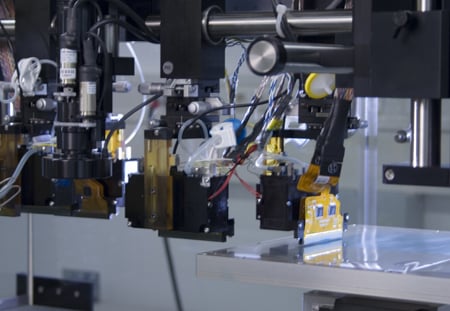
Nanoident circuitry printer head
One of the most prolific uses of this new technology is in medical science, advancing the development of biological sensors and x-ray scanners. It also has industrial and security uses, such reducing the size of and increasing the efficiency of biometric locking devices, the company said.
In addition to any positive uses this new production process may present, it is of course inevitable that it will be also be used for military purposes, Nanoident admitted. Pity.
