This article is more than 1 year old
AMD launches ATI RS690 chipset at long last
Radeon X1200-based integrated 690G arrives
AMD 690G-based motherboards
AMD said many of the usual motherboard suspects will announce 690G- and 690V-based products, with more of the former than the latter. The chipsets support AMD's Sempron and Athlon, single- and dual-core desktop processors.

Asus M2M-VM
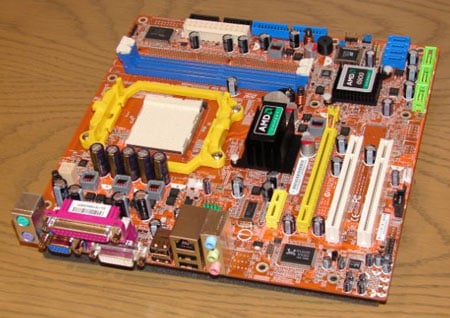
Foxconn A690GM2MA
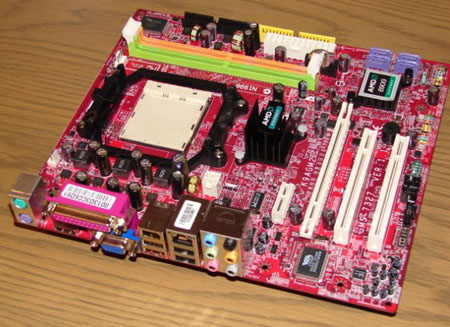
MSI K9MGA2
