This article is more than 1 year old
Good Mobile Messaging 4.9 push email client
Very 'Berry?
Good's strength is its multi-platform support. In addition to Nokia Series 60, there are versions for the Palm Treo 650, 700p, 700w, 700wx and 750v. All HTC's Windows Mobile 5.0 devices are covered, as are their many carrier-branded derivatives. So too are Motorola's Q and HP's hw6500 handsets. It's not a comprehensive list, perhaps, but it covers the latest devices.
Each incarnation has the same look and feel, so should you change smart-phone vendors, you're not only going to be able to re-install the software, but you won't have to learn everything over again. Crucially, all your information is held on Good's server so, again, moving from one device to another is straightforward, as I found when I tried GMM a second time, on a Windows Mobile 5.0-based Vodafone Palm Treo 750v.
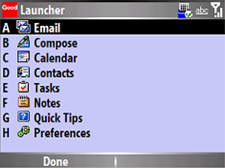
With the software installed, running any of the device's native email and personal information apps calls up Good's code instead, which is run automatically whenever to re-start your handset. It's modular, so you no longer have to leave the host operating system and live in Goodworld, as you did with past versions, though there's a utility, Launcher, that provides a single front-end for all the Good apps, and each app replaces all the usual status icons with GMM's own set.
This separates out email viewing and composition, though you can access the latter from the former, as you'd expect. In addition to Email, GMM incorporates Calendar, Contacts, Tasks and Notes. All five apps have links to the Preferences panel, which is also a Launcher entry, as is Quick Tips, a handy run-through of the features on offer.
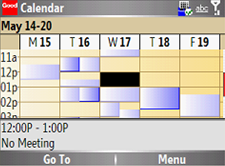
The apps are simple but functional - it reminds me of the early Palm OS. All the data entry basics are covered, just don't expect any fancy customisation options, like adjusting column widths in Email, the creation of extras archive folders, or listing email from the newest to oldest or vice versa - it's newest first only. You can't create multiple calendars for work and home, or different projects. Contacts can't have pictures.
