This article is more than 1 year old
Exec slaps HP with pretexting and Dell hunting charges
While his ex-wife discloses HP’s TV sham
Kamb, of course, sees things very differently from HP.
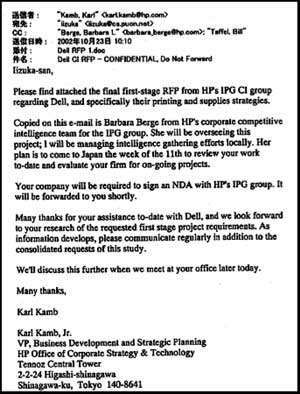
According to his lawsuit, the Japanese chap Iizuka was not a personal consultant helping out with the start-up but rather the informant HP hired to spy on Dell. In addition, Kamb did not take kickbacks from Iizuka or use HP's money to fund his own start-up.
"Due to the highly covert nature of the Dell data collection project, certain persons within HP erroneously assumed that Kamb had misappropriated funds that were intended for Dinner," the lawsuit states. "HP also erroneously believed that Kamb was using those funds to form a competing company. As a result, HP engaged in clandestine acts to obtain Kamb's private telephone records through false pretenses in order to confirm its suspicions."
Kamb claims to have been called by a supposed T-Mobile worker who asked for his PIN number, which Kamb refused to handout. He then called T-Mobile to report the incident and was told T-Mobile had made no such call. Still, "HP obtained access to Kamb's confidential social security number and billing address" through his employee file and used the data to grab his phone records, according to allegations in the lawsuit. Similar incidents occurred with Sprint.
After being visited by HP investigators, Kamb complained to HP's ethics chief and spy scandal star Kevin Hunsaker about the tactics. "Hunsaker purported to speculate that the attempts to access Kamb's phone records were likely perpetrated in connection with his pending divorce proceeding in Texas."
Cough.
Kamb's lawsuit then cites a memo written by HP's lawyers during the spy scandal which states,
Hunsaker first learned that HP had used pretexting to obtain phone records in July 2005 in connection with an unrelated HP investigation. One of the subjects of that investigation was going through a messy divorce, and his attorney contacted Hunsaker claiming that HP had tried to change his PIN to access his voicemail. Hunsaker's team told him they had not altered the subject's PIN or voicemail, but had used pretexting to obtain phone information about the subject.
Cough.
"The claim that pretexting was involved in this investigation is, to the best of our knowledge, patently untrue," HP said in a statement to The Register.
And the lawsuit goes from there to wag a finger at all of HP's spy scandal cast of characters, including Hunsaker, former Chairwoman Patricia Dunn and hired snoop Ron Delia.
The totality of this mess points to how seriously HP took Dell's entry into the printer market, despite public claims to the contrary. The exhibits in Kamb's lawsuit show executives scrounging for every last detail about Dell's rebranded Lexmark products. And, at about this same time, HP employees were in fact complaining about a printer company spying on them.
As the squabbles between HP and Kamb make their way through court, more dripping details are sure to leak out. Sadly for HP, the juicy counterclaims are much more believable these days than they were a few months ago. ®
