This article is more than 1 year old
101 uses for a dead iPhone
In the event of product failure, click here
6: Use it as a personal attack weapon
 Forget the new Taser C2 - the iPhone's aforementioned bullet-proof build makes it the ideal personal defence/attack device.
Forget the new Taser C2 - the iPhone's aforementioned bullet-proof build makes it the ideal personal defence/attack device.
Indeed, in recent computer simulation trials (see picture) an unnamed virtual supermodel inflicted three lawsuits' worth of damage on her anger management counsellor and went on to beat two personal assistants senseless without adverse effect on the iPhone's multifunctional capability.
7: Feed the World™
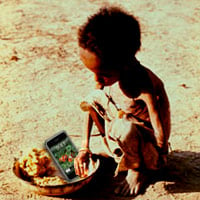 While the Darfur refugee blogosphere has reacted with unbridled enthusiasm to the iPhone's launch ("a seamless melding of music and telecommunications tech, like wow!", as one displaced netizen put it), there's no doubt the device's capabilities could do more to alleviate human suffering worldwide.
While the Darfur refugee blogosphere has reacted with unbridled enthusiasm to the iPhone's launch ("a seamless melding of music and telecommunications tech, like wow!", as one displaced netizen put it), there's no doubt the device's capabilities could do more to alleviate human suffering worldwide.
Accordingly, consider dispatching your iPhone to Africa's poorest and then "let them know it's Christmas" - by SMS. They'll thank you for it, make no mistake.
8: Give it to your girlfriend
 You know how it is: you're away at the Mac developers' conference and the sight of all that hardware is getting the joystick twitching. Trouble is, your other half is 5,000 miles away. What's the plan?
You know how it is: you're away at the Mac developers' conference and the sight of all that hardware is getting the joystick twitching. Trouble is, your other half is 5,000 miles away. What's the plan?
Simple: give her the very latest in interactive iPhone pleasuring device, controlled by you via internet connection and featuring a state-of-the-art iWang™ offering thirteen speeds and gyro-controlled rotational capability. As an added bonus, you can view your efforts in real time as your partner's ecstatic movements are exactly reproduced by her Second Life avatar.
(Please note: Picture is for purpose of illustration only. iWang, connecting cable and girlfriend sold separately.)
9: Use it to solve the planet's energy crisis
 Planet Earth is in crisis, and no messing. With fossil fuel reserves running low and confusion among the world's governments as how best to proceed, we'd like to offer the ultimate clean-energy-generating system: the iPhone superheated atmosphere turbine.
Planet Earth is in crisis, and no messing. With fossil fuel reserves running low and confusion among the world's governments as how best to proceed, we'd like to offer the ultimate clean-energy-generating system: the iPhone superheated atmosphere turbine.
The operational principle is simple: a multi-box Mac set-up via which small groups of Macheads are exposed to screen images of the iPhone, thereby provoking the production of vast quantities of hot air as they bang on relentlessly about how the device has changed their lives and those of their children, and their children's children, etc, etc.
This superheated atmosphere is vented via vast turbines which can produce up to 100kW per geek hour - 70 per cent more efficient than simply burning Apple disciples for fuel. In times of peak demand, extra energy is created by pumping a snap of a sultry Carrie Anne Moss onto an emergency screen, as seen here. To prevent meltdown, one or more of the iPhone images can be removed to cool the reactor's human core.
The iPhone superheated atmosphere turbine generator is fuelled by environmentally-friendly, organic pizza. Note the unspent fuel cell at the bottom left of the picture.
10: Shove it up your...
 No, only joking. Our tenth spot is not a suggestion at all, but rather an invitation - an invitation to those of you recently named by Time magazine as its "Person of the Year", you "citizens of the new digital democracy", to set your fertile Web 2.0 minds to the task as to what exactly the future holds for the Apple iPhone.
No, only joking. Our tenth spot is not a suggestion at all, but rather an invitation - an invitation to those of you recently named by Time magazine as its "Person of the Year", you "citizens of the new digital democracy", to set your fertile Web 2.0 minds to the task as to what exactly the future holds for the Apple iPhone.
We know you won't disappoint us. Get to you blogs. ®
