Dell's love affair with Linux is a clandestine affair these days, conducted in secret, away from disapproving eyes. But now the pair have been spotted in China.
When Michael Dell first saw the web-footed beauty, he fell head over heels. Six years ago Dell pledged a series of strategic investments in Linux companies, including Eazel and Red Hat. The romance attracted the disapproval of Microsoft however, and barely lasted weeks. Very quietly, Dell dumped the bird.
It later emerged that Microsoft's OEM enforcer Joachim Kempin had promised Steve Ballmer that he'd be putting the screws on PC builders, or "hitting the OEMs harder" in his words.
"They should do a delicate dance," wrote Kempin. Microsoft's position was that PC builders should "meet demand but not create demand" for Linux PCs. In a rush to over-compensate, Dell took the "meet demand" edict to comical extremes.
Fifteen months ago our own Ashlee Vance, who broke the news of the first break-up in 2001, proved how hard it is to buy a PC from Dell without Windows. Not pre-loaded with Linux mind you - but simply a bare bones box.
But far away from the prying eyes of Steve Ballmer, romance is blossoming. An eagle-eyed reader found the fruits of the union, brazenly on display in a Beijing subway.
 </
</
That's "Red Flag" Linux, we understand.
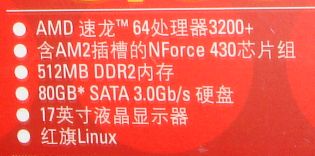
The models advertised here are the Inspiron 1501-n notebook priced at ¥5,199 and ¥5,599, and the Dimension C521-n desktop priced at ¥3,299 and ¥3,999. Both lines feature AMD processors as standard.
If any enterprising readers manage to get a pre-loaded Dell Linux system exported to the USA, let us know.
We hear port security isn't what it should be. It might just get through. ®
Bootnote
Writing in WiReD magazine this month, internet utopian Professor Lawrence Lessig says he now regrets backing antitrust litigation against Microsoft in the 1990s. Lessig had been appointed "special master" in the DoJ's antitrust action, but was harshly thrown off the case when Microsoft discovered an aside he'd made in a private email exchange years previously. Opposing the Beast was "a mistake", says the Prof., because Linux has "changed the business model of Microsoft".
You can see how much it's changed by referring back to our story, How Dell repels attempts to buy its "open source PC". Head for the IM transcript on Page 3.
People have been incarcerated for being less delusional.
