This article is more than 1 year old
Intel intros next-generation Centrino Duo platform
Santa Rosa blooms
IDF Intel has formally announced 'Santa Rosa', the next generation of its Centrino notebook platform, which will incorporate 802.11n Wi-Fi, 'Robson' NAND Flash hard drive cache and GMA X3000 integrated graphics.
It's no surprise that Santa Rosa will feature Core 2 Duo, but this one can run on an 800MHz frontside bus. However, the bus speed can be dynamically reduced and raised according to demand to deliver power savings.
Santa Rosa's 'Crestline' North Bridge chip is now formally named the 965GM. It connects to 533MHz or 667MHZ DDR 2 SDRAM and the platform's ICH8M South Bridge. The 965GM will contain Intel's GMA X3000 integrated graphics engine with Clear Video Technology for piping video data through the pixel shaders.
Santa Rosa will also see the inclusion of a NAND Flash module, codenamed 'Robson', to cache data between the hard drive and memory. Intel said it not only halves application load times but reduces the wake-up-from-sleep time by a similar percentage. Robson yields a 0.4W power saving.
Santa Rosa will also used the latest version of Display Power Saving Technology (DPST), 3.0, to reduce power further. DPST 3.0 automatically switches between progressive and interlaced display modes. again according to the application you're running, saving up to 400mW of power.
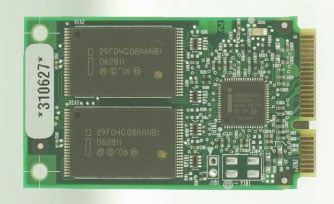
The new Centrino will incorporate Intel's Active Management Technology (AMT) 2.5, tweaked for wireless network connectivity. Santa Rosa will not only incorporate draft 802.11n through a single-sided, two-transmitter, three-receiver MiniPCI card, 'Kedron'.
The platform will also support the 3G WAN card developed jointly by Nokia and Intel. The card will support the HSDPA download speed boost technology.
Both Robson and the 3G WAN module are optional, Intel confirmed - neither is a mandated part of the Centino platform.
Intel is still saying Santa Rosa will ship in H1 2007, though it's expected to come late Q1/early Q2. ®
Read Reg Hardware's complete IDF Fall 06 coverage here
