This article is more than 1 year old
Asus P5B Deluxe Wi-Fi AP motherboard
Core 2 Duo ready
The board layout should be familiar to most Asus devotees as it’s in line with several of their recent offerings. I’m not complaining they worked well and so does this. You’ll need a power supply with a 24-pin ATX power connector and either a four or eight-pin auxiliary power connector. The auxiliary power connector has a protective cap covering four of the eight connectors which must be removed when using an eight-pin plug. This is a clever idea that completely removes the guesswork when using a four-pin power connector.
In expansion terms you’ll find a regular x16 primary PCI Express slot and a secondary Universal x16 PCI Express slot which in reality only supports x4 data mode. ASUS have designed for today rather than tomorrow by supplying just a single x1 slot complimented by three traditional PCI slots. I think this is a sensible move with so few PCI Express cards around at present, but one you don’t quite expect from the company who were so keen to kill off the parallel port on their previous boards.
Six ICH8R South Bridge powered SATA connectors pander to your storage needs with a further two – one to the rear edge of the board and an external port – fed by a JMicron bolt-on controller. This same controller also allows the inclusion of a single dual-channel ATA133/100/66 IDE connector. In an embarrassment of riches both the Intel and the JMicron powered connectors support RAID in modes 0, 1, 5 and 10 with Intel Matrix Storage Technology in the case of the six chipset powered connectors and 0, 1, 0+1 and JBOD from the JMicron controller.
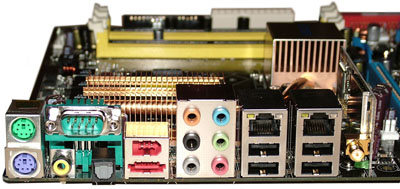
The hardwired external connectors include the customary PS/2 mouse and keyboard connectors alongside which you’ll find a serial port and both coaxial and optical S/PDIF audio outputs.

Next along are the external SATA connector and a FireWire port. A second FireWire port can be added by connecting a supplied bracket to a motherboard header. Four USB ports plus a further two available from a supplied bracket gives you a total of six, with a potential maximum of ten. Headers are supplied for USB ports seven to ten but the header for nine and ten is occupied by the wireless network card.
