This article is more than 1 year old
Core 2 Duo jargon decoder
Intel's dual-core technical talk translated
Viiv
Intel says: "Enjoy your favourite movies, music, games, and more - from the comfort of your couch and controllable with a remote. With the optional TV tuner card and built-in DVR functionality, you can rewind live TV and store all your favourite shows. Online service providers offering access to the latest Hollywood blockbusters, music, games, and more. Download your favourite movies, TV shows, music, games and more, add them to your PC's media library, or record them as a DVD, MP3 or CD. Immerse yourself in home theatre quality 5.1 sound with support for up to 7.1 surround sound. Enjoy support for Intel high-definition video for the entertainment you've purchased and downloaded from the Internet."
We say: Viiv requires a Core 2 Duo or Pentium D dual core processor, a 945, 955, 965 or 975X chipset, HD audio, Windows XP Media Center 2005, Intel Viiv Media Server software and Intel Hub Connect Technology - or to put it another way you need a recent PC with a decent specification. Intel’s strength is the number of deals that it has struck with Hollywood and the record labels. In short, the media companies trust Intel to distribute their content securely with a reasonable degree of DRM to protect their copyright.
Virtualisation Technology
Intel says: "Intel Virtualisation Technology enables one hardware platform to function as multiple "virtual" platforms. In the home, for instance, Intel Virtualisation Technology could enable one family member to be in a room using a PC for gaming while a family member in another room uses a mobile device to simultaneously use the same platform for photo-editing. For businesses, Intel Virtualisation Technology offers improved manageability, limiting downtime and maintaining worker productivity.”
We say: Treating one physical PC as a number of computers is a neat way to handle user accounts so the kids can mess up ‘their’ PC without trashing your photos and e-mail. We can even use virtualisation to create a virtual computer inside a working PC and in the event that it suffers a virus attack then you simply pull the virtual plug and the malware goes up in a puff of smoke. That’s virtual smoke, of course...
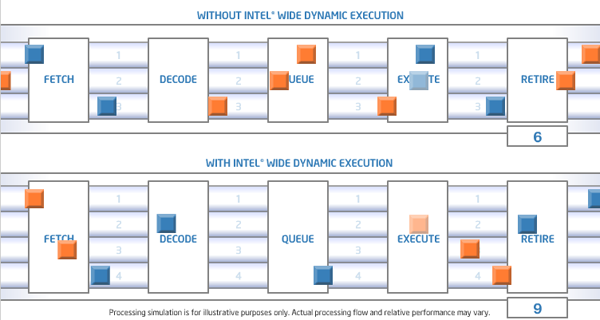
Wide Dynamic Execution
Intel says: "Enables delivery of more instructions per clock cycle to improve execution time and energy efficiency."
We say: Core 2 Duo can begin processing more software instructions at tick of the chip's time-keeping clock than Intel's older chips could. The upshot: more work gets done and your applications run faster. ®