This article is more than 1 year old
MXI Outbacker MXP 40GB biometric hard drive
Serious security
MXI's approach is the more secure of the two, though it has its drawbacks. Each user's protected space is a partition in its own right, so adding more users means re-partitioning the drive. If you've left room, fine - if not, you'll have to zap whatever data existing users have placed on the drive to make room for the new user.
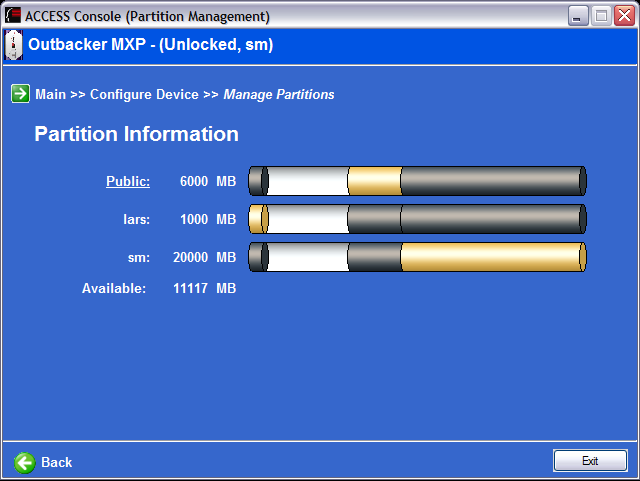
Creating a new users is straightforward: give them a username and get them to enroll a fingerprint. You'll then need to adjust the drive partitions as necessary and, once the user has unlocked his or her space, format it. Like I say, all this 'multiple users, multiple partitions' approach may make for better security, but I prefer LaCie's 'multiple users one drive' system. It's so much easier to manage - surely a mobile drive is only likely to be used by one person in any case? I can imagine more customers wanting a mobile drive that restricts a single data-set to a small number of people, than a drive that assumes each users should only have secure access to his or her own data-set. This latter approach certainly makes sense for a fixed drive that's always connected to a network or a computer, but not a mobile unit.
Connecting the drive to a PC puts three drives in Windows' My Computer list: the public partition, the read-only partition containing the Access software, and third which is where any given user's unlocked space will appear. To unlock the drive on a Windows machine, you have to run Access Unlock - either an installed copy or the one on the drive. Unlike LaCie's software, touching the sensor or attempting to open the locked partition in the usual way doesn't invoke a 'please swipe your fingerprint' request. However, plugging the drive into my MacBook Pro - which is not supported by MXI's software - I found I was able to mount my own partition simply by swiping the sensor with a registered fingerprint.
Re-running Access Unlock simply tells you the drive is already unlocked. To lock it, you have to select the Lock option from the system tray icon's menu. Attempting to unlock a locked drive this way pops up an authentication request. You can either swipe your finger - if it's recognised the drive will automatically open the correct partition - or you can select your username and then swipe to open.
