This article is more than 1 year old
Cassini unravelling origins of Saturn's rings
Cosmic hoops
The origins of some of Saturn's rings' most enigmatic features are becoming clearer, according to scientists analysing the data sent back by the Cassini space craft.
Scientists observed a bright arc of material looping around the edge of the G-ring, one of the most tenuous of all the rings around the gas giant. Researchers now believe this is a long-lived feature of the ring held in place by resonant interactions with the moon Mimas. If so, this would make it strikingly similar to the rings that encircle Neptune.
"We've known since the days of Voyager that we had Jovian-type and Uranian-type rings within the rings of Saturn," said Cassini imaging team leader Dr Carolyn Porco. Dr Porco was the first to work out the dynamics of the Neptunian arcs in Voyager observations. "Now it appears that Saturn may be home to Neptunian-type rings as well."
The researchers had thought the bright arc had formed through a series of collisons between small icy bodies orbiting in the plane of the G-ring. However, they now suspect the arc is actually the source of the G-ring, as particles break away from the arc and drift outwards.
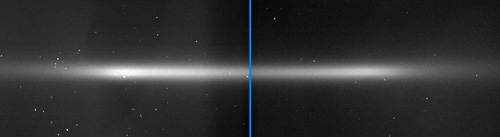
In addition, the research team has learned more about the origins of the E-ring. It is now almost certain that this double banded ring is formed from ice erupting from geysers at the south pole of the moon Enceladus.
To form two bands of material, as shown in the picture above, the particles in the ring must orbit Saturn on inclined orbits, but with a very small range of inclinations.
More research is needed to work out exactly how the double banded structure of the E-ring comes about, but researchers say there are two main scenarios.
First, when the particles are ejected from Enceladus they are already within these restricted parameters and fall naturally into the two bands either side of the ring plane.
Alternatively, they could shoot out of the moon with all kinds of velocities, but particles that end up closer to the ring plane are knocked out of the way (gravitationally scattered) as Enceladus passes through. ®
