This article is more than 1 year old
Beta Pictoris accused of harbouring planets
Dusty ring is a giveaway
The Hubble Space Telescope has found circumstantial evidence for a Jupiter-sized orbiting nearby star, Beta Pictoris, in a new image showing two dust disks orbiting the star.
Scientists have speculated that what appeared to be a warp in the main disk of dust was in fact a second disk. Confirmation of its existence has sparked new speculation that there is at least one gas giant in the stellar system.
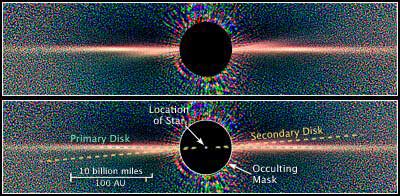
To see the second ring of dust, astronomers had to block the direct light from Beta Pictoris using the (currently offline) Advanced Camera’s coronagraph. The secondary disk, which is inclined at about four degrees from the main disk, is visible as far as 24bn miles from the star, despite being much fainter than the main dust belt.
The best explanation for the disk is that a planet up to 20 times the size of Jupiter is sweeping material out of the main disk as it orbits the star at an incline, NASA said.
"The Hubble observation shows that it is not simply a warp in the dust disk but two concentrations of dust in two separate disks," said lead astronomer David Golimowski of Johns Hopkins University.
"The finding suggests that planets could be forming in two different planes. We know this can happen because the planets in our solar system are typically inclined to Earth's orbit by several degrees. Perhaps stars forming more than one dust disk may be the norm in the formative years of a star system."
Beta Pictoris is 63 light-years away from Earth. The star is much younger that our sun, but it is twice as massive and nine times more luminous.
Because of the age of the star, between 10-20m years, astronomers are confident the dust rings are caused by collisions between planetesimals.
"The actual lifetime of a dust grain is relatively short, maybe a few hundred thousand years," Golimowski said. "So the fact that we can still see these disks around a 10- to 20-million-year-old star means that the dust is being replenished."
Other observations from ground-based telescopes, suggest that a third, unrelated, disk of material orbits the star inside the other two, occupying a region the size of our solar system. This disk is tilted in the other direction, and could be home to other planetary bodies. ®
